Compare commits
59 Commits
infisical-
...
infisical/
| Author | SHA1 | Date | |
|---|---|---|---|
| ebd3d7c7c4 | |||
| 9ecbfe201b | |||
| ba2a03897f | |||
| 304f14c0ed | |||
| 51e5c25e16 | |||
| 0f6490b1e7 | |||
| f894e48fcb | |||
| 37cfa22619 | |||
| 94557344b7 | |||
| d5063018eb | |||
| 51d68505d3 | |||
| 683c512bce | |||
| 43ff28b5fb | |||
| ce41855e84 | |||
| d24461b17c | |||
| 1797e56f9f | |||
| 74f3ca5356 | |||
| db27beaf0b | |||
| d6e55f51f2 | |||
| e9b5996567 | |||
| 094fe73917 | |||
| dc3f85e92e | |||
| c463256058 | |||
| 8df22302fd | |||
| f37fa2bbf5 | |||
| 597c9d6f2a | |||
| 24d2eea930 | |||
| 382cb910af | |||
| 6725475575 | |||
| 026864951b | |||
| 287ed05ab7 | |||
| 37b036e614 | |||
| 024914c168 | |||
| 19e8b6d37b | |||
| b6d648f1f3 | |||
| a514a62a29 | |||
| 2f24956651 | |||
| 13d058025c | |||
| 8ccaa7f29b | |||
| b83964051c | |||
| 0a2b078bdc | |||
| 40d16fa996 | |||
| a3739cfe50 | |||
| a73623258e | |||
| 6da39f41a6 | |||
| 69bbbfcfd8 | |||
| c9d58ec77d | |||
| cb364186d8 | |||
| 918afe05b6 | |||
| e822820151 | |||
| b5ac49eefe | |||
| b21d1a0ed2 | |||
| 70f1122362 | |||
| ea03db8a2c | |||
| 38d9abca17 | |||
| 5bed2580c3 | |||
| d0b899897b | |||
| 1861dc85de | |||
| 68eb0f8dd9 |
@ -108,7 +108,7 @@ brews:
|
||||
zsh_completion.install "completions/infisical.zsh" => "_infisical"
|
||||
fish_completion.install "completions/infisical.fish"
|
||||
man1.install "manpages/infisical.1.gz"
|
||||
- name: 'infisical@{{.Version}}'
|
||||
- name: "infisical@{{.Version}}"
|
||||
tap:
|
||||
owner: Infisical
|
||||
name: homebrew-get-cli
|
||||
@ -186,12 +186,14 @@ aurs:
|
||||
# man pages
|
||||
install -Dm644 "./manpages/infisical.1.gz" "${pkgdir}/usr/share/man/man1/infisical.1.gz"
|
||||
|
||||
# dockers:
|
||||
# - dockerfile: cli/docker/Dockerfile
|
||||
# goos: linux
|
||||
# goarch: amd64
|
||||
# ids:
|
||||
# - infisical
|
||||
# image_templates:
|
||||
# - "infisical/cli:{{ .Version }}"
|
||||
# - "infisical/cli:latest"
|
||||
dockers:
|
||||
- dockerfile: docker/alpine
|
||||
goos: linux
|
||||
goarch: amd64
|
||||
ids:
|
||||
- all-other-builds
|
||||
image_templates:
|
||||
- "infisical/cli:{{ .Version }}"
|
||||
- "infisical/cli:{{ .Major }}.{{ .Minor }}"
|
||||
- "infisical/cli:{{ .Major }}"
|
||||
- "infisical/cli:latest"
|
||||
|
||||
@ -111,11 +111,17 @@ export const createSecretImp = async (req: Request, res: Response) => {
|
||||
authData: req.authData,
|
||||
workspaceId: new Types.ObjectId(workspaceId)
|
||||
});
|
||||
|
||||
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Create,
|
||||
subject(ProjectPermissionSub.Secrets, { environment, secretPath: directory })
|
||||
);
|
||||
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Create,
|
||||
subject(ProjectPermissionSub.Secrets, { environment: secretImport.environment, secretPath: secretImport.secretPath })
|
||||
);
|
||||
|
||||
}
|
||||
|
||||
const folders = await Folder.findOne({
|
||||
@ -323,7 +329,7 @@ export const updateSecretImport = async (req: Request, res: Response) => {
|
||||
authData: req.authData,
|
||||
workspaceId: importSecDoc.workspace
|
||||
});
|
||||
|
||||
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Edit,
|
||||
subject(ProjectPermissionSub.Secrets, {
|
||||
@ -331,6 +337,13 @@ export const updateSecretImport = async (req: Request, res: Response) => {
|
||||
secretPath
|
||||
})
|
||||
);
|
||||
|
||||
secretImports.forEach(({ environment, secretPath }) => {
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Create,
|
||||
subject(ProjectPermissionSub.Secrets, { environment, secretPath })
|
||||
);
|
||||
})
|
||||
}
|
||||
|
||||
const orderBefore = importSecDoc.imports;
|
||||
@ -453,7 +466,7 @@ export const deleteSecretImport = async (req: Request, res: Response) => {
|
||||
authData: req.authData,
|
||||
workspaceId: importSecDoc.workspace
|
||||
});
|
||||
|
||||
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Delete,
|
||||
subject(ProjectPermissionSub.Secrets, {
|
||||
@ -620,7 +633,7 @@ export const getAllSecretsFromImport = async (req: Request, res: Response) => {
|
||||
authData: req.authData,
|
||||
workspaceId: new Types.ObjectId(workspaceId)
|
||||
});
|
||||
|
||||
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Read,
|
||||
subject(ProjectPermissionSub.Secrets, {
|
||||
@ -677,7 +690,7 @@ export const getAllSecretsFromImport = async (req: Request, res: Response) => {
|
||||
authData: req.authData,
|
||||
workspaceId: importSecDoc.workspace
|
||||
});
|
||||
|
||||
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Read,
|
||||
subject(ProjectPermissionSub.Secrets, {
|
||||
|
||||
@ -129,9 +129,14 @@ export const renewAccessToken = async (req: Request, res: Response) => {
|
||||
accessTokenTTL,
|
||||
accessTokenLastRenewedAt,
|
||||
accessTokenMaxTTL,
|
||||
createdAt: accessTokenCreatedAt
|
||||
createdAt: accessTokenCreatedAt,
|
||||
accessTokenNumUses,
|
||||
accessTokenNumUsesLimit
|
||||
} = identityAccessToken;
|
||||
|
||||
if (accessTokenNumUses >= accessTokenNumUsesLimit) {
|
||||
throw BadRequestError({ message: "Unable to renew because access token number of uses limit reached" })
|
||||
}
|
||||
|
||||
// ttl check
|
||||
if (accessTokenTTL > 0) {
|
||||
|
||||
@ -13,7 +13,7 @@ import {
|
||||
ProjectPermissionSub,
|
||||
getAuthDataProjectPermissions
|
||||
} from "../../ee/services/ProjectRoleService";
|
||||
import { ForbiddenError } from "@casl/ability";
|
||||
import { ForbiddenError, subject } from "@casl/ability";
|
||||
import { Types } from "mongoose";
|
||||
|
||||
/**
|
||||
@ -86,6 +86,14 @@ export const createServiceTokenData = async (req: Request, res: Response) => {
|
||||
ProjectPermissionSub.ServiceTokens
|
||||
);
|
||||
|
||||
scopes.forEach(({ environment, secretPath }) => {
|
||||
ForbiddenError.from(permission).throwUnlessCan(
|
||||
ProjectPermissionActions.Create,
|
||||
subject(ProjectPermissionSub.Secrets, { environment, secretPath: secretPath })
|
||||
);
|
||||
})
|
||||
|
||||
|
||||
const secret = crypto.randomBytes(16).toString("hex");
|
||||
const secretHash = await bcrypt.hash(secret, await getSaltRounds());
|
||||
|
||||
|
||||
@ -8,7 +8,10 @@ export enum UserAgentType {
|
||||
WEB = "web",
|
||||
CLI = "cli",
|
||||
K8_OPERATOR = "k8-operator",
|
||||
OTHER = "other"
|
||||
TERRAFORM = "terraform",
|
||||
OTHER = "other",
|
||||
PYTHON_SDK = "InfisicalPythonSDK",
|
||||
NODE_SDK = "InfisicalNodeSDK"
|
||||
}
|
||||
|
||||
export enum EventType {
|
||||
|
||||
@ -10,7 +10,7 @@ export const apiLimiter = rateLimit({
|
||||
// errorHandler: console.error.bind(null, 'rate-limit-mongo')
|
||||
// }),
|
||||
windowMs: 60 * 1000,
|
||||
max: 350,
|
||||
max: 480,
|
||||
standardHeaders: true,
|
||||
legacyHeaders: false,
|
||||
skip: (request) => {
|
||||
@ -30,7 +30,7 @@ const authLimit = rateLimit({
|
||||
// collectionName: "expressRateRecords-authLimit",
|
||||
// }),
|
||||
windowMs: 60 * 1000,
|
||||
max: 100,
|
||||
max: 300,
|
||||
standardHeaders: true,
|
||||
legacyHeaders: false,
|
||||
keyGenerator: (req, res) => {
|
||||
@ -46,8 +46,8 @@ export const passwordLimiter = rateLimit({
|
||||
// errorHandler: console.error.bind(null, 'rate-limit-mongo'),
|
||||
// collectionName: "expressRateRecords-passwordLimiter",
|
||||
// }),
|
||||
windowMs: 60 * 60 * 1000,
|
||||
max: 10,
|
||||
windowMs: 60 * 1000,
|
||||
max: 300,
|
||||
standardHeaders: true,
|
||||
legacyHeaders: false,
|
||||
keyGenerator: (req, res) => {
|
||||
|
||||
@ -7,8 +7,14 @@ export const getUserAgentType = function (userAgent: string | undefined) {
|
||||
return UserAgentType.CLI;
|
||||
} else if (userAgent == UserAgentType.K8_OPERATOR) {
|
||||
return UserAgentType.K8_OPERATOR;
|
||||
} else if (userAgent == UserAgentType.TERRAFORM) {
|
||||
return UserAgentType.TERRAFORM;
|
||||
} else if (userAgent.toLowerCase().includes("mozilla")) {
|
||||
return UserAgentType.WEB;
|
||||
} else if (userAgent.includes(UserAgentType.NODE_SDK)) {
|
||||
return UserAgentType.NODE_SDK;
|
||||
} else if (userAgent.includes(UserAgentType.PYTHON_SDK)) {
|
||||
return UserAgentType.PYTHON_SDK;
|
||||
} else {
|
||||
return UserAgentType.OTHER;
|
||||
}
|
||||
|
||||
@ -158,7 +158,7 @@ export const CreateServiceTokenV2 = z.object({
|
||||
encryptedKey: z.string().trim(),
|
||||
iv: z.string().trim(),
|
||||
tag: z.string().trim(),
|
||||
expiresIn: z.number(),
|
||||
expiresIn: z.number().nullable().optional(),
|
||||
permissions: z.enum(["read", "write"]).array()
|
||||
})
|
||||
});
|
||||
|
||||
@ -1,4 +0,0 @@
|
||||
FROM alpine
|
||||
RUN apk add --no-cache tini
|
||||
COPY infisical /bin/infisical
|
||||
ENTRYPOINT ["/sbin/tini", "--", "/bin/infisical"]
|
||||
9
cli/docker/alpine
Normal file
@ -0,0 +1,9 @@
|
||||
FROM alpine
|
||||
RUN apk add --no-cache tini
|
||||
|
||||
## Upgrade OpenSSL libraries to mitigate known vulnerabilities as the current Alpine image has not been patched yet.
|
||||
RUN apk update && apk upgrade --no-cache libcrypto3 libssl3
|
||||
|
||||
|
||||
COPY infisical /bin/infisical
|
||||
ENTRYPOINT ["/sbin/tini", "--", "/bin/infisical"]
|
||||
@ -11,7 +11,6 @@ import (
|
||||
|
||||
"github.com/Infisical/infisical-merge/packages/models"
|
||||
"github.com/Infisical/infisical-merge/packages/util"
|
||||
"github.com/posthog/posthog-go"
|
||||
"github.com/rs/zerolog/log"
|
||||
"github.com/spf13/cobra"
|
||||
)
|
||||
@ -102,7 +101,7 @@ var exportCmd = &cobra.Command{
|
||||
|
||||
fmt.Print(output)
|
||||
|
||||
Telemetry.CaptureEvent("cli-command:export", posthog.NewProperties().Set("secretsCount", len(secrets)).Set("version", util.CLI_VERSION))
|
||||
// Telemetry.CaptureEvent("cli-command:export", posthog.NewProperties().Set("secretsCount", len(secrets)).Set("version", util.CLI_VERSION))
|
||||
},
|
||||
}
|
||||
|
||||
|
||||
@ -6,6 +6,9 @@ The changelog below reflects new product developments and updates on a monthly b
|
||||
|
||||
## December 2023
|
||||
|
||||
- Released [(machine) identities](https://infisical.com/docs/documentation/platform/identities/overview) and [universal auth](https://infisical.com/docs/documentation/platform/identities/universal-auth) features.
|
||||
- Created new cross-language SDKs for [Python](https://infisical.com/docs/sdks/languages/python), [Node](https://infisical.com/docs/sdks/languages/node), and [Java](https://infisical.com/docs/sdks/languages/java).
|
||||
- Released first version of the [Infisical Agent](https://infisical.com/docs/infisical-agent/overview)
|
||||
- Added ability to [manage folders via CLI](https://infisical.com/docs/cli/commands/secrets).
|
||||
|
||||
## November 2023
|
||||
|
||||
@ -13,7 +13,8 @@ Prerequisites:
|
||||
|
||||
Follow the instructions for your language use the SDK for it:
|
||||
|
||||
- [Node SDK](https://github.com/Infisical/infisical-node)
|
||||
- [Python SDK](https://github.com/Infisical/infisical-python)
|
||||
- [Node SDK](https://infisical.com/docs/sdks/languages/node)
|
||||
- [Python SDK](https://infisical.com/docs/sdks/languages/python)
|
||||
- [Java SDK](https://infisical.com/docs/sdks/languages/java)
|
||||
|
||||
Missing a language? [Throw in a request](https://github.com/Infisical/infisical/issues).
|
||||
@ -240,12 +240,6 @@ At this stage, you know how to use the Infisical-Vercel integration to sync prod
|
||||
|
||||
Check out the [security guide](/security/overview).
|
||||
</Accordion>
|
||||
<Accordion title="Is there way to retain end-to-end encryption for syncing production secrets to Vercel?">
|
||||
Yes. You can also use the Infisical [Node SDK](https://github.com/Infisical/infisical-node) to fetch secrets back to your Next.js app
|
||||
in both development and production.
|
||||
|
||||
Depending on how you use it, however, it may require certain pages to be server-side rendered.
|
||||
</Accordion>
|
||||
</AccordionGroup>
|
||||
|
||||
See also:
|
||||
|
||||
@ -4,8 +4,7 @@ description: "Programmatically interact with Infisical"
|
||||
---
|
||||
|
||||
<Note>
|
||||
Currently, identities can only be used to make authenticated requests to the Infisical API and do not work with any clients such as [Node SDK](https://github.com/Infisical/infisical-node)
|
||||
, [Python SDK](https://github.com/Infisical/infisical-python), CLI, K8s operator, Terraform Provider, etc.
|
||||
Currently, identities can only be used to make authenticated requests to the Infisical API and SDKs. They do not work with clients such as CLI, K8s Operator, Terraform Provider, etc.
|
||||
|
||||
We will be releasing compatibility with it across clients in the coming quarter.
|
||||
</Note>
|
||||
|
||||
@ -12,8 +12,8 @@ This means that updating the value of a base secret propagates directly to other
|
||||
Currently, the secret referencing feature is only supported by the
|
||||
[Infisical CLI](/cli/overview) and [native integrations](/integrations/overview).
|
||||
|
||||
We intend to add support for it to the [Node SDK](https://github.com/Infisical/infisical-node)
|
||||
and [Python SDK](https://github.com/Infisical/infisical-python) this quarter.
|
||||
We intend to add support for it to the [Node SDK](https://infisical.com/docs/sdks/languages/node),
|
||||
[Python SDK](https://infisical.com/docs/sdks/languages/python), and [Java SDK](https://infisical.com/docs/sdks/languages/java) this quarter.
|
||||
</Note>
|
||||
|
||||

|
||||
|
||||
BIN
docs/images/self-hosting/deployment-options/aws-lightsail/awsl-container-service-overview.png
Normal file
|
After 
(image error) Size: 412 KiB |
BIN
docs/images/self-hosting/deployment-options/aws-lightsail/awsl-create-container-service-capacity.png
Normal file
|
After 
(image error) Size: 418 KiB |
BIN
docs/images/self-hosting/deployment-options/aws-lightsail/awsl-create-container-service-deployment.png
Normal file
|
After 
(image error) Size: 359 KiB |
BIN
docs/images/self-hosting/deployment-options/aws-lightsail/awsl-create-container-service-envars.png
Normal file
|
After 
(image error) Size: 334 KiB |
BIN
docs/images/self-hosting/deployment-options/aws-lightsail/awsl-create-container-service-public-endpoint.png
Normal file
|
After 
(image error) Size: 338 KiB |
BIN
docs/images/self-hosting/deployment-options/aws-lightsail/awsl-create-container-service-summary.png
Normal file
|
After 
(image error) Size: 399 KiB |
BIN
docs/images/self-hosting/deployment-options/aws-lightsail/awsl-create-container-service.png
Normal file
|
After 
(image error) Size: 353 KiB |
|
After 
(image error) Size: 402 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-app-service-configuration.png
Normal file
|
After 
(image error) Size: 514 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-app-service-deployment-complete.png
Normal file
|
After 
(image error) Size: 362 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-app-service-overview.png
Normal file
|
After 
(image error) Size: 486 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-create-app-service-basics.png
Normal file
|
After 
(image error) Size: 316 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-create-app-service-docker.png
Normal file
|
After 
(image error) Size: 235 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-create-app-service-review.png
Normal file
|
After 
(image error) Size: 270 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-create-app-service.png
Normal file
|
After 
(image error) Size: 224 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-app-services/aas-select-app-services.png
Normal file
|
After 
(image error) Size: 448 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-container-instance-overview.png
Normal file
|
After 
(image error) Size: 319 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-create-container-instance-advanced.png
Normal file
|
After 
(image error) Size: 258 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-create-container-instance-basics-1.png
Normal file
|
After 
(image error) Size: 302 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-create-container-instance-basics-2.png
Normal file
|
After 
(image error) Size: 290 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-create-container-instance-networking.png
Normal file
|
After 
(image error) Size: 265 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-create-container-instance-review.png
Normal file
|
After 
(image error) Size: 259 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-create-container-instance.png
Normal file
|
After 
(image error) Size: 208 KiB |
BIN
docs/images/self-hosting/deployment-options/azure-container-instances/aci-select-container-instances.png
Normal file
|
After 
(image error) Size: 428 KiB |
BIN
docs/images/self-hosting/deployment-options/gcp-cloud-run/gcp-cloud-run-service-details.png
Normal file
|
After 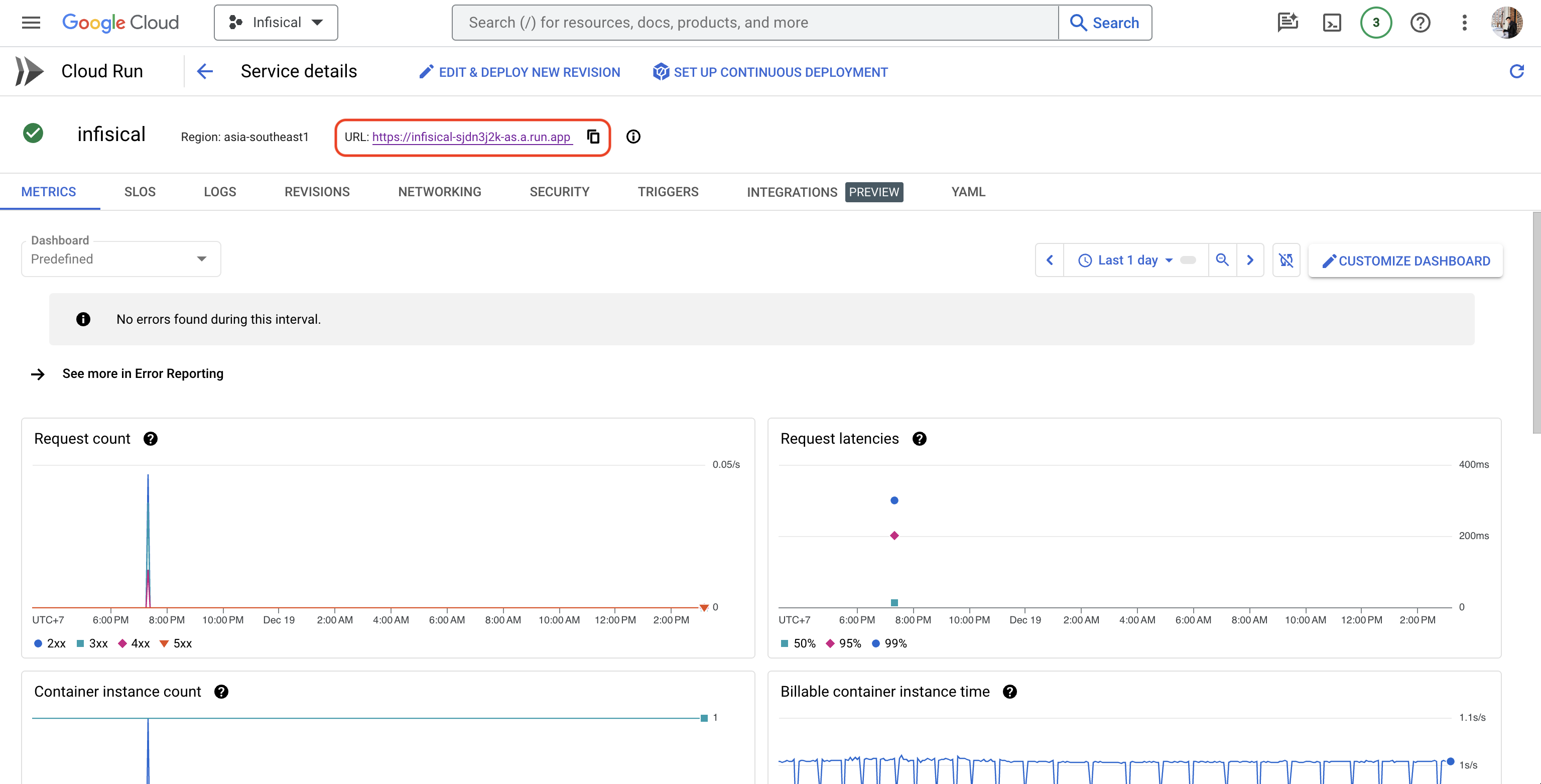
(image error) Size: 294 KiB |
|
After 
(image error) Size: 209 KiB |
BIN
docs/images/self-hosting/deployment-options/railway/railway-deploy-template-infisical.png
Normal file
|
After 
(image error) Size: 191 KiB |
|
After 
(image error) Size: 233 KiB |
BIN
docs/images/self-hosting/deployment-options/railway/railway-infisical-architecture.png
Normal file
|
After 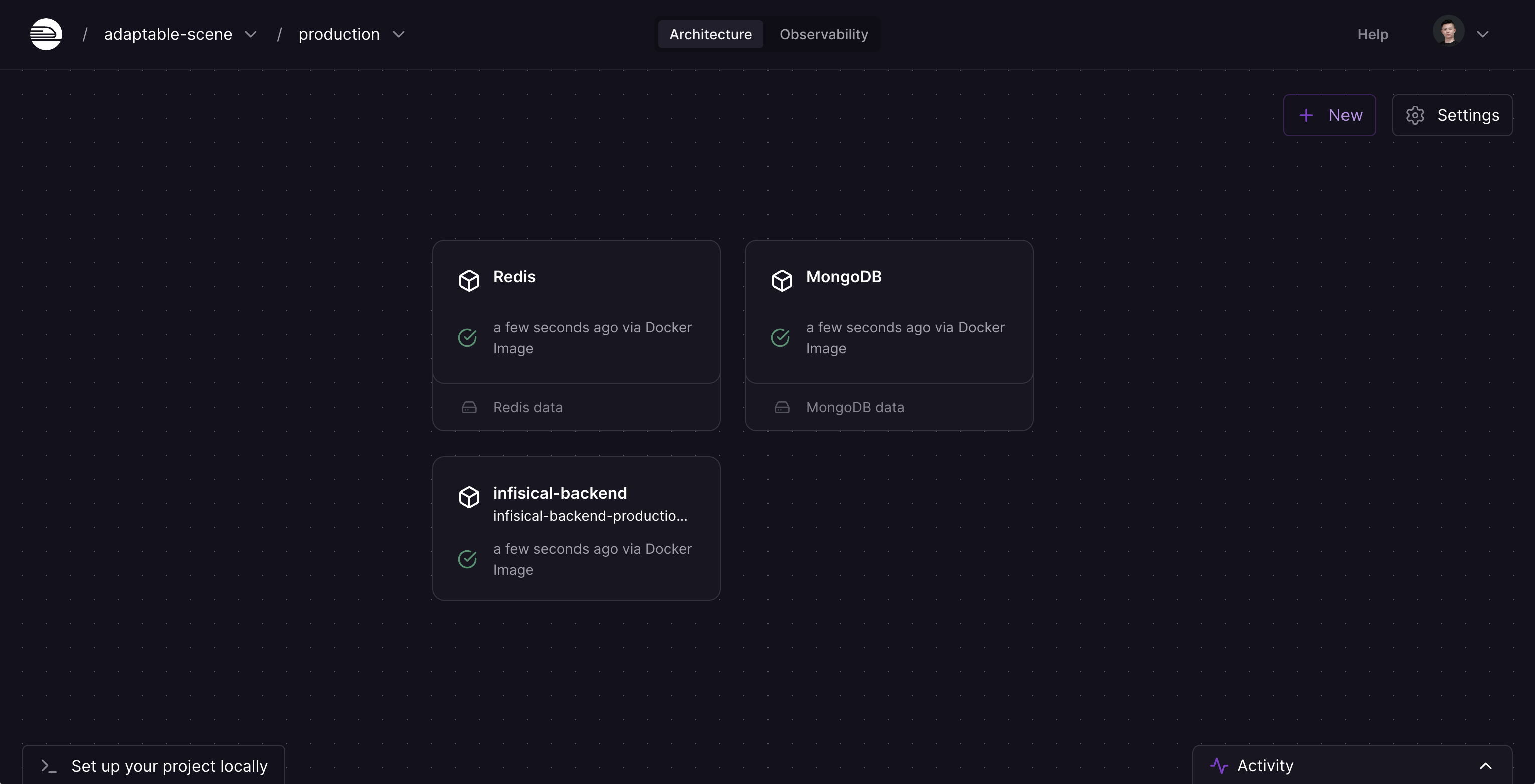
(image error) Size: 233 KiB |
|
After 
(image error) Size: 350 KiB |
|
After 
(image error) Size: 222 KiB |
|
After 
(image error) Size: 198 KiB |
|
After 
(image error) Size: 226 KiB |
|
After 
(image error) Size: 187 KiB |
@ -25,6 +25,6 @@ The Web UI is the browser-based portal that connects to the Infisical API.
|
||||
|
||||
Clients are any application or infrastructure that connecting to the Infisical API using one of the below methods:
|
||||
- Public API: Making API requests directly to the Infisical API.
|
||||
- Client SDK: A platform-specific library with method abstractions for working with secrets. Currently, there are two official SDKs: [Node SDK](https://github.com/Infisical/infisical-node) and [Python SDK](https://github.com/Infisical/infisical-python).
|
||||
- Client SDK: A platform-specific library with method abstractions for working with secrets. Currently, there are three official SDKs: [Node SDK](https://infisical.com/docs/sdks/languages/node), [Python SDK](https://infisical.com/docs/sdks/languages/python), and [Java SDK](https://infisical.com/docs/sdks/languages/java).
|
||||
- CLI: A terminal-based interface for interacting with the Infisical API.
|
||||
- Kubernetes Operator: This operator retrieves secrets from Infisical and securely store
|
||||
@ -159,12 +159,16 @@
|
||||
"pages": [
|
||||
"self-hosting/overview",
|
||||
"self-hosting/deployment-options/standalone-infisical",
|
||||
"self-hosting/deployment-options/docker-compose",
|
||||
"self-hosting/deployment-options/kubernetes-helm",
|
||||
"self-hosting/deployment-options/aws-ec2",
|
||||
"self-hosting/deployment-options/aws-lightsail",
|
||||
"self-hosting/deployment-options/gcp-cloud-run",
|
||||
"self-hosting/deployment-options/docker-compose",
|
||||
"self-hosting/deployment-options/azure-app-services",
|
||||
"self-hosting/deployment-options/azure-container-instances",
|
||||
"self-hosting/deployment-options/digital-ocean-marketplace",
|
||||
"self-hosting/deployment-options/fly.io"
|
||||
"self-hosting/deployment-options/fly.io",
|
||||
"self-hosting/deployment-options/railway"
|
||||
]
|
||||
},
|
||||
"self-hosting/configuration/envars",
|
||||
|
||||
@ -5,5 +5,4 @@ icon: "golang"
|
||||
|
||||
Coming soon.
|
||||
|
||||
Follow this GitHub
|
||||
[issue](https://github.com/Infisical/infisical/issues/436) to stay updated.
|
||||
Star our GitHub repository to stay updated [cross-language SDK](https://github.com/Infisical/sdk) GitHub repository to stay updated.
|
||||
|
||||
@ -3,7 +3,307 @@ title: "Java"
|
||||
icon: "java"
|
||||
---
|
||||
|
||||
Coming soon.
|
||||
If you're working with Java, the official [Infisical Java SDK](https://github.com/Infisical/sdk/tree/main/languages/java) package is the easiest way to fetch and work with secrets for your application.
|
||||
|
||||
Follow this GitHub
|
||||
[issue](https://github.com/Infisical/infisical/issues/434) to stay updated.
|
||||
## Basic Usage
|
||||
|
||||
```java
|
||||
package com.example.app;
|
||||
|
||||
import com.infisical.sdk.InfisicalClient;
|
||||
import com.infisical.sdk.schema.*;
|
||||
|
||||
public class Example {
|
||||
public static void main(String[] args) {
|
||||
// Create a new Infisical Client
|
||||
ClientSettings settings = new ClientSettings();
|
||||
settings.setClientID("MACHINE_IDENTITY_CLIENT_ID");
|
||||
settings.setClientSecret("MACHINE_IDENTITY_CLIENT_SECRET");
|
||||
settings.setCacheTTL(Long.valueOf(300)); // 300 seconds, 5 minutes
|
||||
|
||||
InfisicalClient client = new InfisicalClient(settings);
|
||||
|
||||
// Create the options for fetching the secret
|
||||
GetSecretOptions options = new GetSecretOptions();
|
||||
options.setSecretName("TEST");
|
||||
options.setEnvironment("dev");
|
||||
options.setProjectID("PROJECT_ID");
|
||||
|
||||
// Fetch the sercret with the provided options
|
||||
GetSecretResponseSecret secret = client.getSecret(options);
|
||||
|
||||
// Print the value
|
||||
System.out.println(secret.getSecretValue());
|
||||
|
||||
// Important to avoid memory leaks!
|
||||
// If you intend to use the client throughout your entire application, you can omit this line.
|
||||
client.close();
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
This example demonstrates how to use the Infisical Java SDK in a Java application. The application retrieves a secret named `TEST` from the `dev` environment of the `PROJECT_ID` project.
|
||||
|
||||
<Warning>
|
||||
We do not recommend hardcoding your [Machine Identity Tokens](/platform/identities/overview). Setting it as an environment variable would be best.
|
||||
</Warning>
|
||||
|
||||
# Installation
|
||||
|
||||
The Infisical Java SDK is hosted on the GitHub Packages Apache Maven registry. Because of this you need to configure your environment properly so it's able to pull dependencies from the GitHub registry. Please check [this guide from GitHub](https://docs.github.com/en/packages/working-with-a-github-packages-registry/working-with-the-apache-maven-registry) on how to achieve this.
|
||||
|
||||
Our package is [located here](https://github.com/Infisical/sdk/packages/2019741). Please follow the installation guide on the page.
|
||||
|
||||
# Configuration
|
||||
|
||||
Import the SDK and create a client instance with your [Machine Identity](/platform/identities/universal-auth).
|
||||
|
||||
```java
|
||||
import com.infisical.sdk.InfisicalClient;
|
||||
import com.infisical.sdk.schema.*;
|
||||
|
||||
public class App {
|
||||
public static void main(String[] args) {
|
||||
|
||||
ClientSettings settings = new ClientSettings();
|
||||
settings.setClientID("MACHINE_IDENTITY_CLIENT_ID");
|
||||
settings.setClientSecret("MACHINE_IDENTITY_CLIENT_SECRET");
|
||||
|
||||
InfisicalClient client = new InfisicalClient(settings); // Your client!
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
### ClientSettings methods
|
||||
|
||||
<ParamField query="options" type="object">
|
||||
<Expandable title="properties">
|
||||
<ParamField query="setClientID()" type="string" optional>
|
||||
Your machine identity client ID.
|
||||
</ParamField>
|
||||
<ParamField query="setClientSecret()" type="string" optional>
|
||||
Your machine identity client secret.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="setAccessToken()" type="string" optional>
|
||||
An access token obtained from the machine identity login endpoint.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="setCacheTTL()" type="number" default="300" optional>
|
||||
Time-to-live (in seconds) for refreshing cached secrets.
|
||||
If manually set to 0, caching will be disabled, this is not recommended.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="setSiteURL()" type="string" default="https://app.infisical.com" optional>
|
||||
Your self-hosted absolute site URL including the protocol (e.g. `https://app.infisical.com`)
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
|
||||
</ParamField>
|
||||
|
||||
### Caching
|
||||
|
||||
To reduce the number of API requests, the SDK temporarily stores secrets it retrieves. By default, a secret remains cached for 5 minutes after it's first fetched. Each time it's fetched again, this 5-minute timer resets. You can adjust this caching duration by setting the "cacheTTL" option when creating the client.
|
||||
|
||||
## Working with Secrets
|
||||
|
||||
### client.listSecrets(options)
|
||||
|
||||
```java
|
||||
ListSecretsOptions options = new ListSecretsOptions();
|
||||
options.setEnvironment("dev");
|
||||
options.setProjectID("PROJECT_ID");
|
||||
options.setPath("/foo/bar");
|
||||
options.setIncludeImports(false);
|
||||
|
||||
SecretElement[] secrets = client.listSecrets(options);
|
||||
```
|
||||
|
||||
Retrieve all secrets within the Infisical project and environment that client is connected to
|
||||
|
||||
### Methods
|
||||
|
||||
<ParamField query="Parameters" type="object">
|
||||
<Expandable title="properties">
|
||||
<ParamField query="setEnvironment()" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="setProjectID()" type="string">
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="setPath()" type="string" optional>
|
||||
The path from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="setAttachToProcessEnv()" type="boolean" default="false" optional>
|
||||
Whether or not to set the fetched secrets to the process environment. If true, you can access the secrets like so `System.getenv("SECRET_NAME")`.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="setIncludeImports()" type="boolean" default="false" optional>
|
||||
Whether or not to include imported secrets from the current path. Read about [secret import](/documentation/platform/secret-reference)
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
|
||||
</ParamField>
|
||||
|
||||
### client.getSecret(options)
|
||||
|
||||
```java
|
||||
GetSecretOptions options = new GetSecretOptions();
|
||||
options.setSecretName("TEST");
|
||||
options.setEnvironment("dev");
|
||||
options.setProjectID("PROJECT_ID");
|
||||
|
||||
GetSecretResponseSecret secret = client.getSecret(options);
|
||||
|
||||
String secretValue = secret.getSecretValue();
|
||||
```
|
||||
|
||||
Retrieve a secret from Infisical.
|
||||
|
||||
By default, `getSecret()` fetches and returns a shared secret.
|
||||
|
||||
### Methods
|
||||
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="setSecretName()" type="string" required>
|
||||
The key of the secret to retrieve.
|
||||
</ParamField>
|
||||
<ParamField query="setProjectID()" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="setEnvironment()" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="setPath()" type="string" optional>
|
||||
The path from where secret should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="setType()" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.createSecret(options)
|
||||
|
||||
```java
|
||||
CreateSecretOptions createOptions = new CreateSecretOptions();
|
||||
createOptions.setSecretName("NEW_SECRET");
|
||||
createOptions.setEnvironment("dev");
|
||||
createOptions.setProjectID("PROJECT_ID");
|
||||
createOptions.setSecretValue("SOME SECRET VALUE");
|
||||
createOptions.setPath("/"); // Default
|
||||
createOptions.setType("shared"); // Default
|
||||
|
||||
CreateSecretResponseSecret newSecret = client.createSecret(createOptions);
|
||||
```
|
||||
|
||||
Create a new secret in Infisical.
|
||||
|
||||
### Methods
|
||||
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="setSecretName()" type="string" required>
|
||||
The key of the secret to create.
|
||||
</ParamField>
|
||||
<ParamField query="setSecretValue()" type="string" required>
|
||||
The value of the secret.
|
||||
</ParamField>
|
||||
<ParamField query="setProjectID()" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="setEnvironment()" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="setPath()" type="string" optional>
|
||||
The path from where secret should be created.
|
||||
</ParamField>
|
||||
<ParamField query="setType()" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.updateSecret(options)
|
||||
|
||||
```java
|
||||
UpdateSecretOptions options = new UpdateSecretOptions();
|
||||
|
||||
options.setSecretName("SECRET_TO_UPDATE");
|
||||
options.setSecretValue("NEW SECRET VALUE");
|
||||
options.setEnvironment("dev");
|
||||
options.setProjectID("PROJECT_ID");
|
||||
options.setPath("/"); // Default
|
||||
options.setType("shared"); // Default
|
||||
|
||||
UpdateSecretResponseSecret updatedSecret = client.updateSecret(options);
|
||||
```
|
||||
|
||||
Update an existing secret in Infisical.
|
||||
|
||||
### Methods
|
||||
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="setSecretName()" type="string" required>
|
||||
The key of the secret to update.
|
||||
</ParamField>
|
||||
<ParamField query="setSecretValue()" type="string" required>
|
||||
The new value of the secret.
|
||||
</ParamField>
|
||||
<ParamField query="setProjectID()" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="setEnvironment()" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="setPath()" type="string" optional>
|
||||
The path from where secret should be updated.
|
||||
</ParamField>
|
||||
<ParamField query="setType()" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.deleteSecret(options)
|
||||
|
||||
```java
|
||||
DeleteSecretOptions options = new DeleteSecretOptions();
|
||||
|
||||
options.setSecretName("SECRET_TO_DELETE");
|
||||
options.setEnvironment("dev");
|
||||
options.setProjectID("PROJECT_ID");
|
||||
options.setPath("/"); // Default
|
||||
options.setType("shared"); // Default
|
||||
|
||||
DeleteSecretResponseSecret deletedSecret = client.deleteSecret(options);
|
||||
```
|
||||
|
||||
Delete a secret in Infisical.
|
||||
|
||||
### Methods
|
||||
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="setSecretName()" type="string">
|
||||
The key of the secret to update.
|
||||
</ParamField>
|
||||
<ParamField query="setProjectID()" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="setEnvironment()" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="setPath()" type="string" optional>
|
||||
The path from where secret should be deleted.
|
||||
</ParamField>
|
||||
<ParamField query="setType()" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
@ -3,205 +3,315 @@ title: "Node"
|
||||
icon: "node"
|
||||
---
|
||||
|
||||
If you're working with Node.js, the official [infisical-node](https://github.com/Infisical/infisical-node) package is the easiest way to fetch and work with secrets for your application.
|
||||
If you're working with Node.js, the official [infisical-node](https://github.com/Infisical/sdk/tree/main/languages/node) package is the easiest way to fetch and work with secrets for your application.
|
||||
|
||||
## Basic Usage
|
||||
|
||||
```js
|
||||
import express from "express";
|
||||
import InfisicalClient from "infisical-node";
|
||||
|
||||
import { InfisicalClient, LogLevel } from "@infisical/sdk";
|
||||
|
||||
const app = express();
|
||||
|
||||
const PORT = 3000;
|
||||
|
||||
const client = new InfisicalClient({
|
||||
token: "YOUR_INFISICAL_TOKEN"
|
||||
clientId: "YOUR_CLIENT_ID",
|
||||
clientSecret: "YOUR_CLIENT_SECRET",
|
||||
logLevel: LogLevel.Error
|
||||
});
|
||||
|
||||
app.get("/", async (req, res) => {
|
||||
// access value
|
||||
const name = await client.getSecret("NAME");
|
||||
res.send(`Hello! My name is: ${name.secretValue}`);
|
||||
// access value
|
||||
|
||||
const name = await client.getSecret({
|
||||
environment: "dev",
|
||||
projectId: "PROJECT_ID",
|
||||
path: "/",
|
||||
type: "shared",
|
||||
secretName: "NAME"
|
||||
});
|
||||
|
||||
res.send(`Hello! My name is: ${name.secretValue}`);
|
||||
});
|
||||
|
||||
app.listen(PORT, async () => {
|
||||
console.log(`App listening on port ${PORT}`);
|
||||
// initialize client
|
||||
|
||||
console.log(`App listening on port ${port}`);
|
||||
});
|
||||
```
|
||||
|
||||
This example demonstrates how to use the Infisical Node SDK with an Express application. The application retrieves a secret named "NAME" and responds to requests with a greeting that includes the secret value.
|
||||
|
||||
<Warning>
|
||||
We do not recommend hardcoding your [Infisical
|
||||
Token](/documentation/platform/token). Setting it as an environment
|
||||
variable would be best.
|
||||
We do not recommend hardcoding your [Machine Identity Tokens](/documentation/platform/identities/overview). Setting it as an environment variable
|
||||
would be best.
|
||||
</Warning>
|
||||
|
||||
## Installation
|
||||
|
||||
Run `npm` to add `infisical-node` to your project.
|
||||
Run `npm` to add `@infisical/sdk` to your project.
|
||||
|
||||
```console
|
||||
$ npm install infisical-node --save
|
||||
$ npm install @infisical/sdk
|
||||
```
|
||||
|
||||
## Configuration
|
||||
|
||||
Import the SDK and create a client instance with your [Infisical Token](/documentation/platform/token).
|
||||
Import the SDK and create a client instance with your [Machine Identity](/documentation/platform/identities/overview).
|
||||
|
||||
<Tabs>
|
||||
<Tab title="ES6">
|
||||
```js
|
||||
import InfisicalClient from "infisical-node";
|
||||
|
||||
import { InfisicalClient, LogLevel } from "@infisical/sdk";
|
||||
|
||||
const client = new InfisicalClient({
|
||||
token: "your_infisical_token"
|
||||
clientId: "YOUR_CLIENT_ID",
|
||||
clientSecret: "YOUR_CLIENT_SECRET",
|
||||
logLevel: LogLevel.Error
|
||||
});
|
||||
```
|
||||
|
||||
</Tab>
|
||||
<Tab title="ES5">
|
||||
```js
|
||||
const InfisicalClient = require("infisical-node");
|
||||
|
||||
const { InfisicalClient, LogLevel } = require("@infisical/sdk");
|
||||
|
||||
const client = new InfisicalClient({
|
||||
token: "your_infisical_token"
|
||||
clientId: "YOUR_CLIENT_ID",
|
||||
clientSecret: "YOUR_CLIENT_SECRET",
|
||||
logLevel: LogLevel.Error
|
||||
});
|
||||
````
|
||||
</Tab>
|
||||
|
||||
</Tab>
|
||||
</Tabs>
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="options" type="object">
|
||||
<Expandable title="properties">
|
||||
<ParamField query="token" type="string" optional>
|
||||
An [Infisical Token](/documentation/platform/token) scoped to a project
|
||||
and environment
|
||||
</ParamField>
|
||||
<ParamField
|
||||
query="siteURL"
|
||||
type="string"
|
||||
default="https://app.infisical.com"
|
||||
optional
|
||||
>
|
||||
Your self-hosted absolute site URL including the protocol (e.g.
|
||||
`https://app.infisical.com`)
|
||||
</ParamField>
|
||||
<ParamField query="cacheTTL" type="number" default="300" optional>
|
||||
Time-to-live (in seconds) for refreshing cached secrets. Default: `300`.
|
||||
</ParamField>
|
||||
<ParamField query="debug" type="boolean" default="false" optional>
|
||||
Whether or not debug mode is on
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="clientId" type="string" optional>
|
||||
Your machine identity client ID.
|
||||
</ParamField>
|
||||
<ParamField query="clientSecret" type="string" optional>
|
||||
Your machine identity client secret.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="accessToken" type="string" optional>
|
||||
An access token obtained from the machine identity login endpoint.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="cacheTtl" type="number" default="300" optional>
|
||||
Time-to-live (in seconds) for refreshing cached secrets.
|
||||
If manually set to 0, caching will be disabled, this is not recommended.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="siteUrl" type="string" default="https://app.infisical.com" optional>
|
||||
Your self-hosted absolute site URL including the protocol (e.g. `https://app.infisical.com`)
|
||||
</ParamField>
|
||||
<ParamField query="logLevel" type="enum" default="Error" optional>
|
||||
The level of logs you wish to log The logs are derived from Rust, as we have written our base SDK in Rust.
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
|
||||
</ParamField>
|
||||
|
||||
## Caching
|
||||
### Caching
|
||||
|
||||
The SDK caches every secret and updates it periodically based on the provided `cacheTTL`. For example, if `cacheTTL` of `300` is provided, then a secret will be refetched 5 minutes after the first fetch; if the fetch fails, the cached secret is returned.
|
||||
|
||||
<Tip>
|
||||
For optimal performance, we recommend creating a single instance of the Infisical client and exporting it to be used across your entire app to take advantage of caching benefits.
|
||||
</Tip>
|
||||
To reduce the number of API requests, the SDK temporarily stores secrets it retrieves. By default, a secret remains cached for 5 minutes after it's first fetched. Each time it's fetched again, this 5-minute timer resets. You can adjust this caching duration by setting the "cacheTtl" option when creating the client.
|
||||
|
||||
## Working with Secrets
|
||||
|
||||
### client.getAllSecrets()
|
||||
### client.listSecrets(options)
|
||||
|
||||
```js
|
||||
const secrets = await client.getAllSecrets();
|
||||
const secrets = await client.listSecrets({
|
||||
environment: "dev",
|
||||
projectId: "PROJECT_ID",
|
||||
path: "/foo/bar/",
|
||||
includeImports: false
|
||||
});
|
||||
```
|
||||
|
||||
Retrieve all secrets within the Infisical project and environment that client is connected to
|
||||
|
||||
### client.getSecret(secretName, options)
|
||||
### Parameters
|
||||
|
||||
<ParamField query="Parameters" type="object">
|
||||
<Expandable title="properties">
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="projectId" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="attachToProcessEnv" type="boolean" default="false" optional>
|
||||
Whether or not to set the fetched secrets to the process environment. If true, you can access the secrets like so `process.env["SECRET_NAME"]`.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="includeImports" type="false" default="boolean" optional>
|
||||
Whether or not to include imported secrets from the current path. Read about [secret import](/documentation/platform/secret-reference)
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
|
||||
</ParamField>
|
||||
|
||||
### client.getSecret(options)
|
||||
|
||||
```js
|
||||
const secret = await client.getSecret("API_KEY");
|
||||
const value = secret.secretValue; // get its value
|
||||
const secret = await client.getSecret({
|
||||
environment: "dev",
|
||||
projectId: "PROJECT_ID",
|
||||
secretName: "API_KEY",
|
||||
path: "/",
|
||||
type: "shared"
|
||||
});
|
||||
```
|
||||
|
||||
Retrieve a secret from Infisical.
|
||||
|
||||
By default, `getSecret()` fetches and returns a personal secret. If not found, it returns a shared secret, or tries to retrieve the value from `process.env`. If a secret is fetched, `getSecret()` caches it to reduce excessive calls and re-fetches periodically based on the `cacheTTL` option (default is `300` seconds) when initializing the client — for more information, see the caching section.
|
||||
By default, `getSecret()` fetches and returns a shared secret.
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The key of the secret to retrieve
|
||||
</ParamField>
|
||||
<ParamField query="options" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="type" type="string" default="personal" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal"
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The key of the secret to retrieve.
|
||||
</ParamField>
|
||||
<ParamField query="projectId" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.createSecret(secretName, secretValue, options)
|
||||
### client.createSecret(options)
|
||||
|
||||
```js
|
||||
const newApiKey = await client.createSecret("API_KEY", "FOO");
|
||||
const newApiKey = await client.createSecret({
|
||||
projectId: "PROJECT_ID",
|
||||
environment: "dev",
|
||||
secretName: "API_KEY",
|
||||
secretValue: "SECRET VALUE",
|
||||
path: "/",
|
||||
type: "shared"
|
||||
});
|
||||
```
|
||||
|
||||
Create a new secret in Infisical.
|
||||
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The key of the secret to create
|
||||
</ParamField>
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The value of the secret to create
|
||||
</ParamField>
|
||||
<ParamField query="options" type="object" default="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="type" type="string" default="shared" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". A personal secret can only be created if a shared secret with the same name exists.
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The key of the secret to create.
|
||||
</ParamField>
|
||||
<ParamField query="secretValue" type="string" required>
|
||||
The value of the secret.
|
||||
</ParamField>
|
||||
<ParamField query="projectId" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be created.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.updateSecret(secretName, secretValue, options)
|
||||
### client.updateSecret(options)
|
||||
|
||||
```js
|
||||
const updatedApiKey = await client.updateSecret("API_KEY", "BAR");
|
||||
const updatedApiKey = await client.updateSecret({
|
||||
secretName: "API_KEY",
|
||||
secretValue: "NEW SECRET VALUE",
|
||||
projectId: "PROJECT_ID",
|
||||
environment: "dev",
|
||||
path: "/",
|
||||
type: "shared"
|
||||
});
|
||||
```
|
||||
|
||||
Update an existing secret in Infisical.
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The key of the secret to update
|
||||
</ParamField>
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The new value of the secret
|
||||
</ParamField>
|
||||
<ParamField query="options" type="object" default="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="type" type="string" default="shared" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal"
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The key of the secret to update.
|
||||
</ParamField>
|
||||
<ParamField query="secretValue" type="string" required>
|
||||
The new value of the secret.
|
||||
</ParamField>
|
||||
<ParamField query="projectId" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be updated.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.deleteSecret(secretName, options)
|
||||
### client.deleteSecret(options)
|
||||
|
||||
```js
|
||||
const deletedSecret = await client.deleteSecret("API_KEY");
|
||||
const deletedSecret = await client.deleteSecret({
|
||||
secretName: "API_KEY",
|
||||
|
||||
environment: "dev",
|
||||
projectId: "PROJECT_ID",
|
||||
path: "/",
|
||||
|
||||
type: "shared"
|
||||
});
|
||||
```
|
||||
|
||||
Delete a secret in Infisical.
|
||||
|
||||
<ParamField query="secretName" type="string" required>
|
||||
The key of the secret to delete
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secretName" type="string">
|
||||
The key of the secret to update.
|
||||
</ParamField>
|
||||
<ParamField query="projectId" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be deleted.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
<ParamField query="options" type="object" default="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="type" type="string" default="shared" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". Note that deleting a shared secret also deletes all associated personal secrets.
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
|
||||
|
||||
@ -5,4 +5,4 @@ icon: "php"
|
||||
|
||||
Coming soon.
|
||||
|
||||
Follow this GitHub [issue](https://github.com/Infisical/infisical/issues/531) to stay updated.
|
||||
Star our GitHub repository to stay updated [cross-language SDK](https://github.com/Infisical/sdk) GitHub repository to stay updated.
|
||||
|
||||
@ -3,31 +3,38 @@ title: "Python"
|
||||
icon: "python"
|
||||
---
|
||||
|
||||
If you're working with Python, the official [infisical-python](https://github.com/Infisical/infisical-python) package is the easiest way to fetch and work with secrets for your application.
|
||||
If you're working with Python, the official [infisical-python](https://github.com/Infisical/sdk/edit/main/crates/infisical-py) package is the easiest way to fetch and work with secrets for your application.
|
||||
|
||||
## Basic Usage
|
||||
|
||||
```py
|
||||
from flask import Flask
|
||||
from infisical import InfisicalClient
|
||||
from infisical_client import ClientSettings, InfisicalClient, GetSecretOptions
|
||||
|
||||
app = Flask(__name__)
|
||||
|
||||
client = InfisicalClient(token="your_infisical_token")
|
||||
client = InfisicalClient(ClientSettings(
|
||||
client_id="MACHINE_IDENTITY_CLIENT_ID",
|
||||
client_secret="MACHINE_IDENTITY_CLIENT_SECRET",
|
||||
))
|
||||
|
||||
@app.route("/")
|
||||
def hello_world():
|
||||
# access value
|
||||
name = client.get_secret("NAME")
|
||||
|
||||
name = client.getSecret(options=GetSecretOptions(
|
||||
environment="dev",
|
||||
project_id="PROJECT_ID",
|
||||
secret_name="NAME"
|
||||
))
|
||||
|
||||
return f"Hello! My name is: {name.secret_value}"
|
||||
```
|
||||
|
||||
This example demonstrates how to use the Infisical Python SDK with a Flask application. The application retrieves a secret named "NAME" and responds to requests with a greeting that includes the secret value.
|
||||
|
||||
<Warning>
|
||||
We do not recommend hardcoding your [Infisical
|
||||
Token](/documentation/platform/token). Setting it as an environment
|
||||
variable would be best.
|
||||
We do not recommend hardcoding your [Machine Identity Tokens](/platform/identities/overview). Setting it as an environment variable would be best.
|
||||
</Warning>
|
||||
|
||||
## Installation
|
||||
@ -35,135 +42,244 @@ This example demonstrates how to use the Infisical Python SDK with a Flask appli
|
||||
Run `pip` to add `infisical-python` to your project
|
||||
|
||||
```console
|
||||
$ pip install infisical
|
||||
$ pip install infisical-python
|
||||
```
|
||||
|
||||
Note: You need Python 3.7+.
|
||||
|
||||
## Configuration
|
||||
|
||||
Import the SDK and create a client instance with your [Infisical Token](/documentation/platform/token).
|
||||
Import the SDK and create a client instance with your [Machine Identity](/api-reference/overview/authentication).
|
||||
|
||||
```py
|
||||
from infisical import InfisicalClient
|
||||
from infisical_client import ClientSettings, InfisicalClient
|
||||
|
||||
client = InfisicalClient(token="your_infisical_token")
|
||||
client = InfisicalClient(ClientSettings(
|
||||
client_id="MACHINE_IDENTITY_CLIENT_ID",
|
||||
client_secret="MACHINE_IDENTITY_CLIENT_SECRET",
|
||||
))
|
||||
```
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="token" type="string" optional>
|
||||
An [Infisical Token](/documentation/platform/token) scoped to a project
|
||||
and environment
|
||||
</ParamField>
|
||||
<ParamField
|
||||
query="site_url"
|
||||
type="string"
|
||||
default="https://app.infisical.com"
|
||||
optional
|
||||
>
|
||||
Your self-hosted absolute site URL including the protocol (e.g.
|
||||
`https://app.infisical.com`)
|
||||
</ParamField>
|
||||
<ParamField query="cache_ttl" type="number" default="300" optional>
|
||||
Time-to-live (in seconds) for refreshing cached secrets. Default: `300`.
|
||||
</ParamField>
|
||||
<ParamField query="debug" type="boolean" default="false" optional>
|
||||
Whether or not debug mode is on
|
||||
</ParamField>
|
||||
<ParamField query="options" type="object">
|
||||
<Expandable title="properties">
|
||||
<ParamField query="client_id" type="string" optional>
|
||||
Your Infisical Client ID.
|
||||
</ParamField>
|
||||
<ParamField query="client_secret" type="string" optional>
|
||||
Your Infisical Client Secret.
|
||||
</ParamField>
|
||||
<ParamField query="access_token" type="string" optional>
|
||||
If you want to directly pass an access token obtained from the authentication endpoints, you can do so.
|
||||
</ParamField>
|
||||
|
||||
## Caching
|
||||
<ParamField query="cache_ttl" type="number" default="300" optional>
|
||||
Time-to-live (in seconds) for refreshing cached secrets.
|
||||
If manually set to 0, caching will be disabled, this is not recommended.
|
||||
</ParamField>
|
||||
|
||||
The SDK caches every secret and updates it periodically based on the provided `cache_ttl`. For example, if `cache_ttl` of `300` is provided, then a secret will be refetched 5 minutes after the first fetch; if the fetch fails, the cached secret is returned.
|
||||
|
||||
<Tip>
|
||||
For optimal performance, we recommend creating a single instance of the Infisical client and exporting it to be used across your entire app to take advantage of caching benefits.
|
||||
</Tip>
|
||||
<ParamField
|
||||
query="site_url"
|
||||
type="string"
|
||||
default="https://app.infisical.com"
|
||||
optional
|
||||
>
|
||||
Your self-hosted absolute site URL including the protocol (e.g.
|
||||
`https://app.infisical.com`)
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
|
||||
</ParamField>
|
||||
|
||||
### Caching
|
||||
|
||||
To reduce the number of API requests, the SDK temporarily stores secrets it retrieves. By default, a secret remains cached for 5 minutes after it's first fetched. Each time it's fetched again, this 5-minute timer resets. You can adjust this caching duration by setting the "cache_ttl" option when creating the client.
|
||||
|
||||
## Working with Secrets
|
||||
|
||||
### client.get_all_secrets()
|
||||
### client.listSecrets(options)
|
||||
|
||||
```py
|
||||
secrets = client.get_all_secrets()
|
||||
client.listSecrets(options=ListSecretsOptions(
|
||||
environment="dev",
|
||||
project_id="PROJECT_ID"
|
||||
))
|
||||
```
|
||||
|
||||
Retrieve all secrets within the Infisical project and environment that client is connected to
|
||||
|
||||
### client.get_secret(secret_name, options)
|
||||
### Parameters
|
||||
|
||||
<ParamField query="Parameters" type="object">
|
||||
<Expandable title="properties">
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="project_id" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="attach_to_process_env" type="boolean" default="false" optional>
|
||||
Whether or not to set the fetched secrets to the process environment. If true, you can access the secrets like so `process.env["SECRET_NAME"]`.
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="include_imports" type="boolean" default="false" optional>
|
||||
Whether or not to include imported secrets from the current path. Read about [secret import](/documentation/platform/secret-reference)
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
|
||||
</ParamField>
|
||||
|
||||
### client.getSecret(options)
|
||||
|
||||
```py
|
||||
secret = client.get_secret("API_KEY")
|
||||
secret = client.getSecret(options=GetSecretOptions(
|
||||
environment="dev",
|
||||
project_id="PROJECT_ID",
|
||||
secret_name="API_KEY"
|
||||
))
|
||||
value = secret.secret_value # get its value
|
||||
```
|
||||
|
||||
By default, `get_secret()` fetches and returns a personal secret. If not found, it returns a shared secret, or tries to retrieve the value from `os.environ`. If a secret is fetched, `get_secret()` caches it to reduce excessive calls and re-fetches periodically based on the `cacheTTL` option (default is 300 seconds) when initializing the client — for more information, see the caching section.
|
||||
By default, `getSecret()` fetches and returns a shared secret. If not found, it returns a personal secret.
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="secret_name" type="string" required>
|
||||
The key of the secret to retrieve
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" default="personal" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal"
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secret_name" type="string" required>
|
||||
The key of the secret to retrieve
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="project_id" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "personal".
|
||||
</ParamField>
|
||||
<ParamField query="include_imports" type="boolean" default="false" optional>
|
||||
Whether or not to include imported secrets from the current path. Read about [secret import](/documentation/platform/secret-reference)
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.create_secret(secret_name, secret_value, options)
|
||||
### client.createSecret(options)
|
||||
|
||||
```py
|
||||
new_api_key = client.create_secret("API_KEY", "FOO");
|
||||
api_key = client.createSecret(options=CreateSecretOptions(
|
||||
secret_name="API_KEY",
|
||||
secret_value="Some API Key",
|
||||
environment="dev",
|
||||
project_id="PROJECT_ID"
|
||||
))
|
||||
```
|
||||
|
||||
Create a new secret in Infisical.
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="secret_name" type="string" required>
|
||||
The key of the secret to create
|
||||
</ParamField>
|
||||
<ParamField query="secret_value" type="string" required>
|
||||
The value of the secret to create
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" default="shared" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". A personal secret can only be created if a shared secret with the same name exists.
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secret_name" type="string" required>
|
||||
The key of the secret to create.
|
||||
</ParamField>
|
||||
<ParamField query="secret_value" type="string" required>
|
||||
The value of the secret.
|
||||
</ParamField>
|
||||
<ParamField query="project_id" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be created.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.update_secret(secret_name, secret_value, options)
|
||||
### client.updateSecret(options)
|
||||
|
||||
```py
|
||||
updated_api_key = client.update_secret("API_KEY", "BAR");
|
||||
client.updateSecret(options=UpdateSecretOptions(
|
||||
secret_name="API_KEY",
|
||||
secret_value="NEW_VALUE",
|
||||
environment="dev",
|
||||
project_id="PROJECT_ID"
|
||||
))
|
||||
```
|
||||
|
||||
Update an existing secret in Infisical.
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="secret_name" type="string" required>
|
||||
The key of the secret to update
|
||||
</ParamField>
|
||||
<ParamField query="secret_value" type="string" required>
|
||||
The new value of the secret
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" default="shared" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal"
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secret_name" type="string" required>
|
||||
The key of the secret to update.
|
||||
</ParamField>
|
||||
<ParamField query="secret_value" type="string" required>
|
||||
The new value of the secret.
|
||||
</ParamField>
|
||||
<ParamField query="project_id" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be updated.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
|
||||
### client.delete_secret(secret_name, options)
|
||||
### client.deleteSecret(options)
|
||||
|
||||
```py
|
||||
deleted_secret = client.delete_secret("API_KEY");
|
||||
client.deleteSecret(options=DeleteSecretOptions(
|
||||
environment="dev",
|
||||
project_id="PROJECT_ID",
|
||||
secret_name="API_KEY"
|
||||
))
|
||||
```
|
||||
|
||||
Delete a secret in Infisical.
|
||||
|
||||
### Parameters
|
||||
|
||||
<ParamField query="secret_name" type="string" required>
|
||||
The key of the secret to delete
|
||||
<ParamField query="Parameters" type="object" optional>
|
||||
<Expandable title="properties">
|
||||
<ParamField query="secret_name" type="string">
|
||||
The key of the secret to update.
|
||||
</ParamField>
|
||||
<ParamField query="project_id" type="string" required>
|
||||
The project ID where the secret lives in.
|
||||
</ParamField>
|
||||
<ParamField query="environment" type="string" required>
|
||||
The slug name (dev, prod, etc) of the environment from where secrets should be fetched from.
|
||||
</ParamField>
|
||||
<ParamField query="path" type="string" optional>
|
||||
The path from where secret should be deleted.
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal". If not specified, the default value is "shared".
|
||||
</ParamField>
|
||||
</Expandable>
|
||||
</ParamField>
|
||||
<ParamField query="type" type="string" default="shared" optional>
|
||||
The type of the secret. Valid options are "shared" or "personal"
|
||||
</ParamField>
|
||||
|
||||
Follow this GitHub
|
||||
[issue](https://github.com/Infisical/infisical/issues/433) to stay updated.
|
||||
|
||||
@ -5,5 +5,4 @@ icon: "gem"
|
||||
|
||||
Coming soon.
|
||||
|
||||
Follow this GitHub
|
||||
[issue](https://github.com/Infisical/infisical/issues/435) to stay updated.
|
||||
Star our GitHub repository to stay updated [cross-language SDK](https://github.com/Infisical/sdk) GitHub repository to stay updated.
|
||||
|
||||
@ -5,5 +5,4 @@ icon: "rust"
|
||||
|
||||
Coming soon.
|
||||
|
||||
Follow this GitHub
|
||||
[issue](https://github.com/Infisical/infisical/issues/437) to stay updated.
|
||||
Star our GitHub repository to stay updated [cross-language SDK](https://github.com/Infisical/sdk) GitHub repository to stay updated.
|
||||
|
||||
@ -2,104 +2,52 @@
|
||||
title: "Introduction"
|
||||
---
|
||||
|
||||
From local development to production, Infisical SDKs provide the easiest way for your app to fetch back secrets from Infisical on demand.
|
||||
From local development to production, Infisical SDKs provide the easiest way for your app to fetch back secrets from Infisical on demand.
|
||||
|
||||
- Install and initialize a language-specific client SDK into your application
|
||||
- Provision the client scoped-access to a project and environment in Infisical
|
||||
- Fetch secrets on demand
|
||||
- Install and initialize a language-specific client SDK into your application
|
||||
- Provision the client scoped-access to a project and environment in Infisical
|
||||
- Fetch secrets on demand
|
||||
|
||||
<CardGroup cols={2}>
|
||||
<Card
|
||||
title="Node"
|
||||
href="https://github.com/Infisical/infisical-node"
|
||||
icon="node"
|
||||
color="#68a063"
|
||||
>
|
||||
Manage secrets for your Node application on demand
|
||||
</Card>
|
||||
<Card
|
||||
href="https://github.com/Infisical/infisical-python"
|
||||
title="Python"
|
||||
icon="python"
|
||||
color="#4c8abe"
|
||||
>
|
||||
Manage secrets for your Python application on demand
|
||||
</Card>
|
||||
<Card
|
||||
href="/sdks/languages/java"
|
||||
title="Java"
|
||||
icon="java"
|
||||
color="#e41f23"
|
||||
>
|
||||
Manage secrets for your Java application on demand
|
||||
</Card>
|
||||
<Card
|
||||
href="/sdks/languages/ruby"
|
||||
title="Ruby"
|
||||
icon="gem"
|
||||
color="#ac0d01"
|
||||
>
|
||||
Manage secrets for your Ruby application on demand
|
||||
</Card>
|
||||
<Card
|
||||
href="/sdks/languages/go"
|
||||
title="Golang"
|
||||
icon="golang"
|
||||
color="#00add8"
|
||||
>
|
||||
Manage secrets for your Go application on demand
|
||||
</Card>
|
||||
<Card
|
||||
href="/sdks/languages/rust"
|
||||
title="Rust"
|
||||
icon="rust"
|
||||
color="#cd412b"
|
||||
>
|
||||
Manage secrets for your Rust application on demand
|
||||
</Card>
|
||||
<Card
|
||||
href="/sdks/languages/php"
|
||||
title="PHP"
|
||||
icon="php"
|
||||
color="#787cb4"
|
||||
>
|
||||
Manage secrets for your PHP application on demand
|
||||
</Card>
|
||||
<Card title="Node" href="/sdks/languages/node" icon="node" color="#68a063">
|
||||
Manage secrets for your Node application on demand
|
||||
</Card>
|
||||
<Card href="/sdks/languages/python" title="Python" icon="python" color="#4c8abe">
|
||||
Manage secrets for your Python application on demand
|
||||
</Card>
|
||||
<Card href="/sdks/languages/java" title="Java" icon="java" color="#e41f23">
|
||||
Manage secrets for your Java application on demand
|
||||
</Card>
|
||||
<Card href="/sdks/languages/ruby" title="Ruby" icon="gem" color="#ac0d01">
|
||||
Manage secrets for your Ruby application on demand
|
||||
</Card>
|
||||
<Card href="/sdks/languages/go" title="Golang" icon="golang" color="#00add8">
|
||||
Manage secrets for your Go application on demand
|
||||
</Card>
|
||||
<Card href="/sdks/languages/rust" title="Rust" icon="rust" color="#cd412b">
|
||||
Manage secrets for your Rust application on demand
|
||||
</Card>
|
||||
<Card href="/sdks/languages/php" title="PHP" icon="php" color="#787cb4">
|
||||
Manage secrets for your PHP application on demand
|
||||
</Card>
|
||||
</CardGroup>
|
||||
|
||||
## FAQ
|
||||
|
||||
<AccordionGroup>
|
||||
<Accordion title="Are my secrets exposed in transit every time the SDK fetches them?">
|
||||
No. Infisical uses end-to-end encryption which ensures that secrets are always encrypted in transit
|
||||
and decrypted on the client side. In fact, not even the server can decrypt your secrets (unless
|
||||
that permission is explicitly granted from within the platform).
|
||||
|
||||
Check out the [security guide](/security/overview).
|
||||
</Accordion>
|
||||
<Accordion title="Isn't it inefficient if my app makes a request every time it needs a secret?">
|
||||
The client SDK caches every secret and implements a 5-minute waiting period before
|
||||
re-requesting it. The waiting period can be controlled by setting the `cacheTTL` parameter at
|
||||
the time of initializing the client.
|
||||
The client SDK caches every secret and implements a 5-minute waiting period before re-requesting it. The waiting period can be controlled by
|
||||
setting the `cacheTTL` parameter at the time of initializing the client.
|
||||
|
||||
Note: The exact parameter name may differ depending on the language.
|
||||
</Accordion>
|
||||
<Accordion title="Can I attach the environment variables to my process environment?">
|
||||
Yes you can! The client SDK provides a method to attach the secrets to your process environment. When using the `listSecrets()` method, you
|
||||
can pass a `attachToProcessEnv` parameter, which tells the SDK to attach all the found secrets to your process environment.
|
||||
|
||||
Note: The exact parameter name may differ depending on the language.
|
||||
</Accordion>
|
||||
<Accordion title="What if a request for a secret fails?">
|
||||
The SDK caches every secret and falls back to the cached value if a request fails. If no cached
|
||||
value ever-existed, the SDK falls back to whatever value is on `process.env`.
|
||||
The SDK caches every secret and falls back to the cached value if a request fails. If no cached value is found, and the request fails, then the SDK throws an error.
|
||||
</Accordion>
|
||||
<Accordion title="Can I still use process.env with the SDK?">
|
||||
Yes. If no `token` parameter is passed in at the time of initializing the client or nothing is found when requesting for a secret,
|
||||
then the SDK falls back to whatever value is on `process.env`.
|
||||
</Accordion>
|
||||
<Accordion title="What's the point if I still have to manage a token for the SDK?">
|
||||
The token enables the SDK to authenticate with Infisical to fetch back your secrets.
|
||||
Although the SDK requires you to pass in a token, it enables greater efficiency and security
|
||||
than if you managed dozens of secrets yourself without it. Here're some benefits:
|
||||
|
||||
- You always pull in the right secrets because they're fetched on demand from a centralize source that is Infisical.
|
||||
- You can use the Infisical which comes with tons of benefits like secret versioning, access controls, audit logs, etc.
|
||||
- You now risk leaking one token that can be revoked instead of dozens of raw secrets.
|
||||
|
||||
And much more.
|
||||
</Accordion>
|
||||
|
||||
</AccordionGroup>
|
||||
</AccordionGroup>
|
||||
|
||||
66
docs/self-hosting/deployment-options/aws-lightsail.mdx
Normal file
@ -0,0 +1,66 @@
|
||||
---
|
||||
title: "AWS Lightsail"
|
||||
description: "Deploy Infisical with AWS Lightsail"
|
||||
---
|
||||
|
||||
Prerequisites:
|
||||
- Have an account with [Amazon Web Services (AWS)](https://aws.amazon.com/)
|
||||
|
||||
<Steps>
|
||||
<Step title="Create a container service in AWS Lightsail">
|
||||
1.1. In AWS, navigate to the **Lightsail** service and press **Create container service** under the **Containers** tab.
|
||||

|
||||
|
||||

|
||||
|
||||
1.2. In the **Container service location** section, select the AWS region that's closest to your infrastructure.
|
||||
|
||||
Afterwards, in the **Container service capacity** section, set the power level and scale to fit your needs; you may opt for the default setting
|
||||
and adjust accordingly in the future.
|
||||
|
||||

|
||||
|
||||
1.3. In the **Set up your first deployment** section, select the **Specify a custom deployment** option. Give the container a friendly name like **infisical** and fill in your intended [Infisical public Docker image](https://hub.docker.com/r/infisical/infisical) in the **Image** field; this will pull the image from Docker Hub.
|
||||
|
||||
For example, in order to opt for Infisical `v0.43.4`, you would input: `infisical/infisical:v0.43.4`.
|
||||
|
||||

|
||||
|
||||
1.4. Running Infisical requires a few environment variables to be set for the container service.
|
||||
At minimum, Infisical requires that you set the variables `ENCRYPTION_KEY`, `AUTH_SECRET`, `MONGO_URL`, and `REDIS_URL`
|
||||
which you can read more about [here](/self-hosting/configuration/envars).
|
||||
|
||||
In the **Environment variables** section, fill in the required environment variables.
|
||||
|
||||
<Note>
|
||||
To use more features like emailing and single sign-on, you can set additional configuration options [here](/self-hosting/configuration/envars).
|
||||
</Note>
|
||||
|
||||
Also, under the **Open ports** section, add an entry for port `8080` and protocol `HTTP` since Infisical listens on port `8080`.
|
||||
|
||||

|
||||
|
||||
1.5. In the **Public endpoint** section, select the container from the previous steps from the dropdown; this will make the container accessible over the public internet.
|
||||
|
||||

|
||||
|
||||
1.6. Finally, in the **Identify your service** section, give the container service a unique name like infisical and press **Create container service**.
|
||||
|
||||

|
||||
</Step>
|
||||
<Step title="Navigate to your deployed instance of Infisical">
|
||||
On the newly-created container service page, wait for the **Status** to turn to **Running** and check out the **Public domain** of the container service; you can access your instance of Infisical by this URL.
|
||||
|
||||

|
||||
</Step>
|
||||
</Steps>
|
||||
|
||||
<AccordionGroup>
|
||||
<Accordion title="Do you have any recommendations for deploying Infisical with AWS Lightsail?">
|
||||
Yes, here are a few that come to mind:
|
||||
- In step 1.3, we recommend pinning the Docker image to a specific [version of Infisical](https://hub.docker.com/r/infisical/infisical/tags)
|
||||
instead of referring to the `latest` tag to avoid any unexpected version-to-version migration issues.
|
||||
|
||||
We're working on putting together a fuller list of deployment best practices as well as minimum resource configuration requirements for running Infisical so stay tuned!
|
||||
</Accordion>
|
||||
</AccordionGroup>
|
||||
71
docs/self-hosting/deployment-options/azure-app-services.mdx
Normal file
@ -0,0 +1,71 @@
|
||||
---
|
||||
title: "Azure App Services"
|
||||
description: "Deploy Infisical with Azure App Service"
|
||||
---
|
||||
|
||||
Prerequisites:
|
||||
- Have an account with [Microsoft Azure](https://azure.microsoft.com/en-us)
|
||||
|
||||
<Steps>
|
||||
<Step title="Create a Web App in Azure App Services">
|
||||
1.1. In Azure, navigate to the **App Services** solution and press **Create > Web App**.
|
||||
|
||||

|
||||
|
||||

|
||||
|
||||
1.2. In the **Basics** section, specify the **Subscription** and **Resource group** to manage the deployed resource.
|
||||
|
||||
Also, give the container a friendly name like Infisical and specify a **Region** for it to be deployed to.
|
||||
|
||||

|
||||
|
||||
1.3. In the **Docker** section, select the **Single Container** option under **Options** and specify **Docker Hub** as the image source
|
||||
|
||||
Next, under the **Docker hub options** sub-section, select the **Public** option under **Access Type** and fill in your intended [Infisical public Docker image](https://hub.docker.com/r/infisical/infisical) in the **Image and tag** field; this will pull the image from Docker Hub.
|
||||
|
||||
For example, in order to opt for Infisical `v0.43.4`, you would input: `infisical/infisical:v0.43.4`.
|
||||
|
||||

|
||||
|
||||
1.4. Finally, in the **Review + create** section, double check the information from the previous steps and press **Create** to create the Azure app service.
|
||||
|
||||

|
||||
|
||||
1.5. Next, wait a minute or two on the deployment overview page for the app to be created. Once the deployment is complete, press **Go to resource**
|
||||
to head to the **App Service dashboard** for the newly-created app.
|
||||
|
||||

|
||||
|
||||
1.6. Running Infisical requires a few environment variables to be set for the Azure app service.
|
||||
At minimum, Infisical requires that you set the variables `ENCRYPTION_KEY`, `AUTH_SECRET`, `MONGO_URL`, and `REDIS_URL`
|
||||
which you can read more about [here](/self-hosting/configuration/envars).
|
||||
|
||||
<Note>
|
||||
To use more features like emailing and single sign-on, you can set additional configuration options [here](/self-hosting/configuration/envars).
|
||||
</Note>
|
||||
|
||||
Additionally, you must set the variable `WEBSITES_PORT=8080` since
|
||||
Infisical listens on port `8080`.
|
||||
|
||||
In the **Settings > Configuration** section of the newly-created app service, fill in the required environment variables.
|
||||
|
||||

|
||||
</Step>
|
||||
<Step title="Navigate to your deployed instance of Infisical">
|
||||
In the **Overview** section, check out the **Default domain** for your instance of Infisical; you can visit the instance at this URL.
|
||||
|
||||

|
||||
</Step>
|
||||
</Steps>
|
||||
|
||||
<AccordionGroup>
|
||||
<Accordion title="Do you have any recommendations for deploying Infisical with Azure App Services?">
|
||||
Yes, here are a few that come to mind:
|
||||
- In step 1.3, we recommend pinning the Docker image to a specific [version of Infisical](https://hub.docker.com/r/infisical/infisical/tags)
|
||||
instead of referring to the `latest` tag to avoid any unexpected version-to-version migration issues.
|
||||
- In step 1.2, we recommend selecting a **Region** option that is closest to your infrastructure/clients to reduce latency.
|
||||
|
||||
We're working on putting together a fuller list of deployment best practices as well as minimum resource configuration requirements for running Infisical so stay tuned!
|
||||
</Accordion>
|
||||
</AccordionGroup>
|
||||
@ -0,0 +1,88 @@
|
||||
---
|
||||
title: "Azure Container Instances"
|
||||
description: "Deploy Infisical with Azure Container Instances"
|
||||
---
|
||||
|
||||
Prerequisites:
|
||||
- Have an account with [Microsoft Azure](https://azure.microsoft.com/en-us)
|
||||
|
||||
<Note>
|
||||
This brief goes over how to deploy an instance of Infisical with Azure Container Instances without TLS/SSL configuration.
|
||||
|
||||
There are various options for enabling TLS/SSL with Azure Container Instances more suitable for production including:
|
||||
- [Enabling a TLS endpoint in a sidecar container](https://learn.microsoft.com/en-us/azure/container-instances/container-instances-container-group-ssl).
|
||||
- [Enabling automatic HTTPS with Caddy in a sidecar container](https://learn.microsoft.com/en-us/azure/container-instances/container-instances-container-group-automatic-ssl).
|
||||
- Using Azure Function Proxies, Application Gateway, etc.
|
||||
|
||||
For a simpler deployment experience with complete TLS/SSL setup, you may try [deploying Infisical with Azure App Services](/self-hosting/deployment-options/azure-app-services).
|
||||
</Note>
|
||||
|
||||
<Steps>
|
||||
<Step title="Create a container instance in Azure Container Instances">
|
||||
1.1. In Azure, navigate to the **Container Instances** solution and press **Create**.
|
||||
|
||||

|
||||
|
||||

|
||||
|
||||
1.2. In the **Basics** section, specify the **Subscription** and **Resource group** to manage the deployed resource.
|
||||
|
||||
Also, give the container a friendly name like Infisical and specify a **Region** for it to be deployed to.
|
||||
|
||||

|
||||
|
||||
Next, select the **Public** option under **Image type** and fill in your intended [Infisical public Docker image](https://hub.docker.com/r/infisical/infisical) in the **Image** field; this will pull the image from Docker Hub.
|
||||
|
||||
For example, in order to opt for Infisical `v0.43.4`, you would input: `infisical/infisical:v0.43.4`.
|
||||
|
||||

|
||||
|
||||
<Note>
|
||||
Depending on your use-case and requirements, you may find it helpful to further configure your Azure container instance.
|
||||
|
||||
For example, you may want to adjust the **Region** option to specify which region to deploy the container for your
|
||||
instance of Infisical to minimize distance and therefore latency between the instance and your infrastructure.
|
||||
</Note>
|
||||
|
||||
1.3. In the **Networking** section, select the **Public** option under **Networking type**; this will make the container accessible over the public internet.
|
||||
|
||||
Next, under the **Ports** section, add an entry for port `8080` and protocol `TCP` since Infisical listens on port `8080`.
|
||||
|
||||

|
||||
|
||||
1.4. Running Infisical requires a few environment variables to be set for the Azure container instance.
|
||||
At minimum, Infisical requires that you set the variables `ENCRYPTION_KEY`, `AUTH_SECRET`, `MONGO_URL`, and `REDIS_URL`
|
||||
which you can read more about [here](/self-hosting/configuration/envars).
|
||||
|
||||
In the **Advanced** section, fill in the required environment variables.
|
||||
|
||||
<Note>
|
||||
To use more features like emailing and single sign-on, you can set additional configuration options [here](/self-hosting/configuration/envars).
|
||||
</Note>
|
||||
|
||||

|
||||
|
||||
1.5. Finally, in the **Review + create** section, double check the information from the previous steps and press **Create** to create the Azure container instance.
|
||||
|
||||

|
||||
</Step>
|
||||
<Step title="Navigate to your deployed instance of Infisical">
|
||||
Head to the **Overview** page of the newly-created container instance to view its **IP address (Public)**; you can access your instance of Infisical by this IP address under the port `:8080`.
|
||||
|
||||
For example, in the image below, the IP address of the sample deployed container instance is `4.255.87.109`; the instance would be accessible in the browser by heading to `4.255.87.109:8080`.
|
||||
|
||||

|
||||
</Step>
|
||||
</Steps>
|
||||
|
||||
<AccordionGroup>
|
||||
<Accordion title="Do you have any recommendations for deploying Infisical with Azure Container Instances?">
|
||||
Yes, here are a few that come to mind:
|
||||
- In step 1.2, we recommend pinning the Docker image to a specific [version of Infisical](https://hub.docker.com/r/infisical/infisical/tags)
|
||||
instead of referring to the `latest` tag to avoid any unexpected version-to-version migration issues.
|
||||
- In step 1.2, we recommend selecting a **Region** option that is closest to your infrastructure/clients to reduce latency.
|
||||
- Enable TLS/SSL with Azure Container Instances. There are various options for doing so including [enabling a TLS endpoint in a sidecar container](https://learn.microsoft.com/en-us/azure/container-instances/container-instances-container-group-ssl), [enabling automatic HTTPS with Caddy in a sidecar container](https://learn.microsoft.com/en-us/azure/container-instances/container-instances-container-group-automatic-ssl), and using Azure Function Proxies, Application Gateway, etc.
|
||||
|
||||
We're working on putting together a fuller list of deployment best practices as well as minimum resource configuration requirements for running Infisical so stay tuned!
|
||||
</Accordion>
|
||||
</AccordionGroup>
|
||||
@ -1,51 +1,54 @@
|
||||
---
|
||||
title: "Docker Compose"
|
||||
description: "Learn to install Infisical using our Docker Compose template"
|
||||
description: "Run Infisical with Docker Compose template"
|
||||
---
|
||||
|
||||
## Install Docker on your VM
|
||||
<Steps>
|
||||
<Step title="Install Docker on your VM">
|
||||
```bash
|
||||
# Example in ubuntu
|
||||
apt-get update
|
||||
apt-get upgrade
|
||||
apt install docker-compose
|
||||
```
|
||||
</Step>
|
||||
<Step title="Download required files">
|
||||
2.1. Run the command below to download the `.env` file template.
|
||||
|
||||
```bash
|
||||
wget -O .env https://raw.githubusercontent.com/Infisical/infisical/main/.env.example
|
||||
```
|
||||
|
||||
2.2. Run the command below to download the docker compose template.
|
||||
|
||||
```bash
|
||||
wget -O docker-compose.yml https://raw.githubusercontent.com/Infisical/infisical/main/docker-compose.yml
|
||||
```
|
||||
|
||||
2.3. Run the command below to download the `nginx` config file.
|
||||
|
||||
```bash
|
||||
mkdir nginx && wget -O ./nginx/default.conf https://raw.githubusercontent.com/Infisical/infisical/main/nginx/default.dev.conf
|
||||
```
|
||||
|
||||
</Step>
|
||||
<Step title="Update the .env file">
|
||||
Running Infisical requires a few environment variables to be set.
|
||||
At minimum, Infisical requires that you set the variables `ENCRYPTION_KEY`, `AUTH_SECRET`, `MONGO_URL`, and `REDIS_URL` which you can read more about [here](/self-hosting/configuration/envars).
|
||||
|
||||
```bash
|
||||
# Example in ubuntu
|
||||
apt-get update
|
||||
apt-get upgrade
|
||||
apt install docker-compose
|
||||
```
|
||||
Tweak the `.env` accordingly.
|
||||
|
||||
## Download the required files
|
||||
```bash
|
||||
nano .env
|
||||
```
|
||||
</Step>
|
||||
<Step title="Start Infisical">
|
||||
Finally, run the command below to get Infisical up and running (in detached mode).
|
||||
|
||||
```bash
|
||||
# Download env file template
|
||||
wget -O .env https://raw.githubusercontent.com/Infisical/infisical/main/.env.example
|
||||
```bash
|
||||
docker-compose -f docker-compose.yml up -d
|
||||
```
|
||||
|
||||
# Download docker compose template
|
||||
wget -O docker-compose.yml https://raw.githubusercontent.com/Infisical/infisical/main/docker-compose.yml
|
||||
|
||||
# Download nginx config
|
||||
mkdir nginx && wget -O ./nginx/default.conf https://raw.githubusercontent.com/Infisical/infisical/main/nginx/default.dev.conf
|
||||
```
|
||||
|
||||
## Update .env file
|
||||
Tweak the `.env` according to your preferences. Refer to the available [environment variables](/self-hosting/configuration/envars)
|
||||
|
||||
```bash
|
||||
# update environment variables like mongo login
|
||||
nano .env
|
||||
```
|
||||
|
||||
<Info>
|
||||
Infisical assumes that you have configured HTTPS. If you didn't configure HTTPS, set `HTTPS_ENABLED` to `false` in the .env file to avoid frequent logouts.
|
||||
</Info>
|
||||
|
||||
## Get the service up and running
|
||||
|
||||
```bash
|
||||
# Start up services in detached mode
|
||||
docker-compose -f docker-compose.yml up -d
|
||||
```
|
||||
|
||||
Your Infisical installation is complete and should be running on [http://localhost:80](http://localhost:80). Please note that the containers are not exposed to the internet and only bind to the localhost. It's up to you to configure a firewall, SSL certificates, and implement any additional security measures.
|
||||
|
||||
<Info>
|
||||
Once installation is complete, you will have to create the first account. No default account is provided.
|
||||
</Info>
|
||||
Your Infisical installation is complete and should be running on port `80` or `http://localhost:80`.
|
||||
</Step>
|
||||
</Steps>
|
||||
@ -23,7 +23,7 @@ Prerequisites:
|
||||
|
||||
2.2. In the service creation form, select the **Deploy one revision from an existing container image** option and fill in your intended [Infisical public Docker image](https://hub.docker.com/r/infisical/infisical) in the container image URL.
|
||||
|
||||
For example, in order to opt for Infisical `v0.43.4`, you would use the following URL: `docker.io/infisical/infisical:v0.43.4`.
|
||||
For example, in order to opt for Infisical `v0.43.4`, you would input: `docker.io/infisical/infisical:v0.43.4`.
|
||||
|
||||

|
||||
|
||||
@ -48,6 +48,11 @@ Prerequisites:
|
||||
|
||||
Finally, press **Create** to finish setting up the GCP Cloud Run service.
|
||||
</Step>
|
||||
<Step title="Navigate to your deployed instance of Infisical">
|
||||
Head to the **Service details** of the newly-created service to view its URL; you can access your instance of Infisical by clicking on the URL.
|
||||
|
||||

|
||||
</Step>
|
||||
</Steps>
|
||||
|
||||
<AccordionGroup>
|
||||
@ -59,5 +64,4 @@ Prerequisites:
|
||||
|
||||
We're working on putting together a fuller list of deployment best practices as well as minimum resource configuration requirements for running Infisical so stay tuned!
|
||||
</Accordion>
|
||||
</AccordionGroup>
|
||||
|
||||
</AccordionGroup>
|
||||
@ -161,4 +161,3 @@ Once installation is complete, you will have to create the first account. No def
|
||||
|
||||
## Related blogs
|
||||
- [Set up Infisical in a development cluster](https://iamunnip.hashnode.dev/infisical-open-source-secretops-kubernetes-setup)
|
||||
- [Set up Infisical in AKS using ArgoCD + Helm and integrate with an application using kustomize](https://mrdevops.medium.com/infisical-open-source-secretops-apply-it-using-gitops-approach-245f57fcd67e)
|
||||
|
||||
61
docs/self-hosting/deployment-options/railway.mdx
Normal file
@ -0,0 +1,61 @@
|
||||
---
|
||||
title: "Railway"
|
||||
description: "Deploy Infisical with Railway"
|
||||
---
|
||||
|
||||
Prerequisites:
|
||||
- Have an account with [Railway](https://railway.app/)
|
||||
|
||||
<Steps>
|
||||
<Step title="Deploy the Infisical template with Railway">
|
||||
1.1. In Railway, create a new project and select **Deploy a template > Infisical**.
|
||||
|
||||

|
||||
|
||||

|
||||
|
||||

|
||||
|
||||

|
||||
|
||||
1.2. At minimum, Infisical requires that you set the variables `ENCRYPTION_KEY`, `AUTH_SECRET`, `MONGO_URL`, and `REDIS_URL`
|
||||
which you can read more about [here](/self-hosting/configuration/envars).
|
||||
|
||||
By default, the Infisical template on Railway pre-configures environment variables on each service in the deployment but requires you to supply two for the Redis and MongoDB services.
|
||||
|
||||
On the MongoDB service, supply a value for the `MONGO_INITDB_ROOT_PASSWORD` variable.
|
||||
|
||||

|
||||
|
||||
On the Redis service, supply a value for the `REDIS_PASSWORD` variable.
|
||||
|
||||

|
||||
|
||||

|
||||
|
||||
<Note>
|
||||
To use more features like emailing and single sign-on, you can set additional configuration options on the Infisical service [here](/self-hosting/configuration/envars).
|
||||
</Note>
|
||||
|
||||
Finally, press **Deploy** to create the project and deploy the services within it.
|
||||
|
||||

|
||||
|
||||

|
||||
</Step>
|
||||
<Step title="Navigate to your deployed instance of Infisical">
|
||||
Head to the newly-created Infisical service to view its URL under Networking > Public Networking; you can access your instance of Infisical by clicking on the URL.
|
||||
|
||||

|
||||
</Step>
|
||||
</Steps>
|
||||
|
||||
<AccordionGroup>
|
||||
<Accordion title="Do you have any recommendations for deploying Infisical with Railway?">
|
||||
Yes, here are a few that come to mind:
|
||||
- While the Infisical template on Railway uses the `latest` tag to get the latest version of Infisical, we recommend creating a Railway deployment that pins the Docker image to a specific [version of Infisical](https://hub.docker.com/r/infisical/infisical/tags) to avoid any unexpected version-to-version migration issues.
|
||||
- We recommend selecting **Deployment region** options for your Railway service deployments to be closest to your infrastructure/clients to reduce latency.
|
||||
|
||||
We're working on putting together a fuller list of deployment best practices as well as minimum resource configuration requirements for running Infisical so stay tuned!
|
||||
</Accordion>
|
||||
</AccordionGroup>
|
||||
@ -1,63 +1,49 @@
|
||||
---
|
||||
title: "Docker"
|
||||
description: "Learn to install Infisical purely on docker"
|
||||
description: "Run Infisical with Docker"
|
||||
---
|
||||
|
||||
The Infisical standalone version combines all the essential components into a single container, making deployment and management more straightforward than other methods.
|
||||
Prerequisites:
|
||||
- Basic knowledge of [Docker](https://www.docker.com/)
|
||||
- Have Docker installed on your system. If not, follow the installation guide [here](https://docs.docker.com/get-docker/).
|
||||
|
||||
## Prerequisites
|
||||
|
||||
This guide assumes you have basic knowledge of Docker and have it installed on your system. If you don't have Docker installed, please follow the official installation guide [here](https://docs.docker.com/get-docker/).
|
||||
|
||||
#### System requirements
|
||||
To have a functional deployment, we recommended compute with **2GB of RAM** and **1 CPU**.
|
||||
However, depending on your usage, you may need to further scale up system resources to meet demand.
|
||||
|
||||
## Pull the Infisical Docker image
|
||||
|
||||
Open your terminal or command prompt and enter the following command to pull the Infisical Docker image:
|
||||
|
||||
```
|
||||
docker pull infisical/infisical:latest
|
||||
```
|
||||
|
||||
## Run with docker
|
||||
To run Infisical, we'll need to configure the required configs listed below.
|
||||
Other configs can be found [here](../configuration/envars)
|
||||
<Steps>
|
||||
<Step title="Pull the Infisical Docker image">
|
||||
Run the following command in your terminal to pull the Infisical Docker image:
|
||||
|
||||
<ParamField query="ENCRYPTION_KEY" type="string" default="none" required>
|
||||
Must be a random 16 byte hex string. Can be generated with `openssl rand -hex 16`
|
||||
</ParamField>
|
||||
```
|
||||
docker pull infisical/infisical:latest
|
||||
```
|
||||
</Step>
|
||||
<Step title="Start Infisical">
|
||||
2.1. Running Infisical requires a few environment variables to be set.
|
||||
At minimum, Infisical requires that you set the variables `ENCRYPTION_KEY`, `AUTH_SECRET`, `MONGO_URL`, and `REDIS_URL`
|
||||
which you can read more about [here](/self-hosting/configuration/envars).
|
||||
|
||||
Once you have added the required environment variables to your docker run command, execute it in your terminal to get Infisical up and running.
|
||||
|
||||
For example:
|
||||
|
||||
<ParamField query="AUTH_SECRET" type="string" default="none" required>
|
||||
Must be a random 32 byte base64 string. Can be generated with `openssl rand -base64 32`
|
||||
</ParamField>
|
||||
```bash
|
||||
docker run -p 80:8080 \
|
||||
-e ENCRYPTION_KEY=f40c9178624764ad85a6830b37ce239a \
|
||||
-e AUTH_SECRET="q6LRi7c717a3DQ8JUxlWYkZpMhG4+RHLoFUVt3Bvo2U=" \
|
||||
-e MONGO_URL="<>" \
|
||||
infisical/infisical:latest
|
||||
```
|
||||
|
||||
<Warning>
|
||||
The above environment variable values are only to be used as an example and should not be used in production
|
||||
</Warning>
|
||||
|
||||
2.2. Once the container is running, verify the installation by opening your web browser and navigating to `http://localhost:80`.
|
||||
</Step>
|
||||
</Steps>
|
||||
|
||||
<ParamField query="MONGO_URL" type="string" default="none" required>
|
||||
*TLS based connection string is not yet supported
|
||||
</ParamField>
|
||||
|
||||
<ParamField query="REDIS_URL" type="string" default="none" required>
|
||||
Redis connection string
|
||||
</ParamField>
|
||||
|
||||
Once you have added the required environment variables to your docker run command, execute it in your terminal.
|
||||
|
||||
```bash
|
||||
docker run -p 80:8080 \
|
||||
-e ENCRYPTION_KEY=f40c9178624764ad85a6830b37ce239a \
|
||||
-e AUTH_SECRET=5239fea3a4720c0e524f814a540e14a2 \
|
||||
-e MONGO_URL="<>" \
|
||||
infisical/infisical:latest
|
||||
```
|
||||
|
||||
<Warning>
|
||||
The above environment variable values are only to be used as an example and should not be used in production
|
||||
</Warning>
|
||||
|
||||
## Verify the installation:
|
||||
Once the container is running, open a web browser and navigate to http://localhost:80. That's it! You have successfully installed the Infisical application using a single Docker image.
|
||||
|
||||
<Info>
|
||||
Once installation is complete, you will have to create the first account. No default account is provided.
|
||||
</Info>
|
||||
<AccordionGroup>
|
||||
<Accordion title="What are the system requirements for running Infisical?">
|
||||
To have a functional deployment, we recommended compute with 2GB of RAM and 1 CPU.
|
||||
|
||||
However, depending on your usage, you may need to further scale up system resources to meet demand.
|
||||
</Accordion>
|
||||
</AccordionGroup>
|
||||
@ -1,10 +1,9 @@
|
||||
---
|
||||
title: "Introduction"
|
||||
description: "Explore deployment options for self hosting Infisical"
|
||||
description: "Self-host Infisical on your own infrastructure"
|
||||
---
|
||||
|
||||
To meet various compliance requirements, you may want to self-host Infisical instead of using [Infisical Cloud](https://app.infisical.com/).
|
||||
Self-hosted Infisical allows you to maintain your sensitive information within your own infrastructure and network, ensuring complete control over your data.
|
||||
Self-hosting Infisical lets you retain data on your own infrastructure and network.
|
||||
Choose from a variety of deployment options listed below to get started.
|
||||
|
||||
<Card
|
||||
@ -22,9 +21,6 @@ Choose from a variety of deployment options listed below to get started.
|
||||
>
|
||||
Automatically create and deploy Infisical on to a Kubernetes cluster
|
||||
</Card>
|
||||
<Card title="AWS EC2" color="#0285c7" href="deployment-options/aws-ec2">
|
||||
Install infisical with just a few clicks using our Cloud Formation template
|
||||
</Card>
|
||||
<Card
|
||||
title="Docker Compose"
|
||||
color="#0285c7"
|
||||
@ -39,12 +35,19 @@ Choose from a variety of deployment options listed below to get started.
|
||||
>
|
||||
Use our Helm chart to Install Infisical on your Kubernetes cluster
|
||||
</Card>
|
||||
<Card
|
||||
title="Fly.io"
|
||||
color="#ea5a0c"
|
||||
href="deployment-options/fly.io"
|
||||
<Card
|
||||
title="AWS EC2"
|
||||
color="#0285c7"
|
||||
href="deployment-options/aws-ec2"
|
||||
>
|
||||
Deploy Infisical with Fly.io
|
||||
Install infisical with just a few clicks using our Cloud Formation template
|
||||
</Card>
|
||||
<Card
|
||||
title="AWS Lightsail"
|
||||
color="#0285c7"
|
||||
href="deployment-options/aws-lightsail"
|
||||
>
|
||||
Deploy Infisical with AWS Lightsail
|
||||
</Card>
|
||||
<Card
|
||||
title="GCP Cloud Run"
|
||||
@ -53,4 +56,32 @@ Choose from a variety of deployment options listed below to get started.
|
||||
>
|
||||
Deploy Infisical with GCP Cloud Run
|
||||
</Card>
|
||||
<Card
|
||||
title="Azure App Services"
|
||||
color="#ea5a0c"
|
||||
href="deployment-options/azure-app-services"
|
||||
>
|
||||
Deploy Infisical with Azure App Services
|
||||
</Card>
|
||||
<Card
|
||||
title="Azure Container Instances"
|
||||
color="#ea5a0c"
|
||||
href="deployment-options/azure-container-instances"
|
||||
>
|
||||
Deploy Infisical with Azure Container Instances
|
||||
</Card>
|
||||
<Card
|
||||
title="Fly.io"
|
||||
color="#ea5a0c"
|
||||
href="deployment-options/fly.io"
|
||||
>
|
||||
Deploy Infisical with Fly.io
|
||||
</Card>
|
||||
<Card
|
||||
title="Railway"
|
||||
color="#ea5a0c"
|
||||
href="deployment-options/railway"
|
||||
>
|
||||
Deploy Infisical with Railway
|
||||
</Card>
|
||||
</CardGroup>
|
||||
|
||||
@ -50,5 +50,8 @@ export const userAgentTTypeoNameMap: { [K in UserAgentType]: string } = {
|
||||
[UserAgentType.WEB]: "Web",
|
||||
[UserAgentType.CLI]: "CLI",
|
||||
[UserAgentType.K8_OPERATOR]: "K8s operator",
|
||||
[UserAgentType.TERRAFORM]: "Terraform",
|
||||
[UserAgentType.NODE_SDK]: "InfisicalNodeSDK",
|
||||
[UserAgentType.PYTHON_SDK]: "InfisicalPythonSDK",
|
||||
[UserAgentType.OTHER]: "Other",
|
||||
};
|
||||
@ -8,6 +8,9 @@ export enum UserAgentType {
|
||||
WEB = "web",
|
||||
CLI = "cli",
|
||||
K8_OPERATOR = "k8-operator",
|
||||
TERRAFORM = "terraform",
|
||||
NODE_SDK = "node-sdk",
|
||||
PYTHON_SDK = "python-sdk",
|
||||
OTHER = "other"
|
||||
}
|
||||
|
||||
|
||||
@ -716,6 +716,12 @@ export const AppLayout = ({ children }: LayoutProps) => {
|
||||
</a>
|
||||
</DropdownMenuItem>
|
||||
))}
|
||||
{infisicalPlatformVersion && (
|
||||
<div className="cursor-default mb-2 mt-2 w-full pl-5 duration-200 hover:text-mineshaft-200 text-sm">
|
||||
<FontAwesomeIcon icon={faInfo} className="mr-4 px-[0.1rem]" />
|
||||
Version: {infisicalPlatformVersion}
|
||||
</div>
|
||||
)}
|
||||
</DropdownMenuContent>
|
||||
</DropdownMenu>
|
||||
{subscription &&
|
||||
@ -745,12 +751,6 @@ export const AppLayout = ({ children }: LayoutProps) => {
|
||||
</div>
|
||||
</button>
|
||||
)}
|
||||
{infisicalPlatformVersion && (
|
||||
<div className="mb-2 w-full pl-5 duration-200 hover:text-mineshaft-200">
|
||||
<FontAwesomeIcon icon={faInfo} className="mr-4 px-[0.1rem]" />
|
||||
Version: {infisicalPlatformVersion}
|
||||
</div>
|
||||
)}
|
||||
</div>
|
||||
</nav>
|
||||
</aside>
|
||||
|
||||
@ -56,7 +56,7 @@ export default function VercelCreateIntegrationPage() {
|
||||
appId: targetAppId
|
||||
});
|
||||
|
||||
const filteredBranches = branches?.filter((branchName) => branchName !== "main").concat("");
|
||||
const filteredBranches = branches?.filter((branchName) => branchName !== "main").concat();
|
||||
|
||||
useEffect(() => {
|
||||
if (workspace) {
|
||||
@ -125,7 +125,7 @@ export default function VercelCreateIntegrationPage() {
|
||||
subTitle="Select which environment or folder in Infisical you want to sync to Vercel's environment variables."
|
||||
>
|
||||
<div className="flex flex-row items-center">
|
||||
<div className="inline flex items-center">
|
||||
<div className="flex items-center">
|
||||
<Image
|
||||
src="/images/integrations/Vercel.png"
|
||||
height={30}
|
||||
|
||||
@ -67,8 +67,16 @@ const features = [
|
||||
{
|
||||
_id: 0,
|
||||
name: "Kubernetes Operator",
|
||||
link: "https://infisical.com/docs/documentation/getting-started/kubernetes",
|
||||
description:
|
||||
"Pull secrets into your Kubernetes containers and automatically redeploy upon secret changes."
|
||||
},
|
||||
{
|
||||
_id: 1,
|
||||
name: "Infisical Agent",
|
||||
link: "https://infisical.com/docs/infisical-agent/overview",
|
||||
description:
|
||||
"Inject secrets into your apps without modifying any application logic."
|
||||
}
|
||||
];
|
||||
|
||||
@ -691,11 +699,44 @@ const OrganizationPage = withPermission(
|
||||
</div>
|
||||
)}
|
||||
</div>
|
||||
<div className="mb-4 flex flex-col items-start justify-start px-6 py-6 pb-6 text-3xl">
|
||||
<p className="mr-4 font-semibold text-white">Explore Infisical</p>
|
||||
<div className="mt-4 grid grid-cols-3 w-full gap-4">
|
||||
{features.map((feature) => (
|
||||
<div
|
||||
key={feature._id}
|
||||
className="flex h-44 w-full flex-col justify-between rounded-md border border-mineshaft-600 bg-mineshaft-800 p-4"
|
||||
>
|
||||
<div className="mt-0 text-lg text-mineshaft-100">{feature.name}</div>
|
||||
<div className="mb-4 mt-2 text-[15px] font-light text-mineshaft-300">
|
||||
{feature.description}
|
||||
</div>
|
||||
<div className="flex w-full items-center">
|
||||
<div className="text-[15px] font-light text-mineshaft-300">
|
||||
Setup time: 20 min
|
||||
</div>
|
||||
<a
|
||||
target="_blank"
|
||||
rel="noopener noreferrer"
|
||||
className="group ml-auto w-max cursor-default rounded-full border border-mineshaft-600 bg-mineshaft-900 py-2 px-4 text-sm text-mineshaft-300 hover:border-primary-500/80 hover:bg-primary-800/20 hover:text-mineshaft-200"
|
||||
href={feature.link}
|
||||
>
|
||||
Learn more{" "}
|
||||
<FontAwesomeIcon
|
||||
icon={faArrowRight}
|
||||
className="pl-1.5 pr-0.5 duration-200 group-hover:pl-2 group-hover:pr-0"
|
||||
/>
|
||||
</a>
|
||||
</div>
|
||||
</div>
|
||||
))}
|
||||
</div>
|
||||
</div>
|
||||
{!(
|
||||
new Date().getTime() - new Date(user?.createdAt).getTime() <
|
||||
30 * 24 * 60 * 60 * 1000
|
||||
) && (
|
||||
<div className="mb-4 flex flex-col items-start justify-start px-6 py-6 pb-0 text-3xl">
|
||||
<div className="mb-4 flex flex-col items-start justify-start px-6 pb-6 pb-0 text-3xl">
|
||||
<p className="mr-4 mb-4 font-semibold text-white">Onboarding Guide</p>
|
||||
<div className="mb-3 grid w-full grid-cols-1 gap-3 lg:grid-cols-2 xl:grid-cols-3 2xl:grid-cols-4">
|
||||
<LearningItemSquare
|
||||
@ -784,42 +825,6 @@ const OrganizationPage = withPermission(
|
||||
)}
|
||||
</div>
|
||||
)}
|
||||
<div className="mb-4 flex flex-col items-start justify-start px-6 py-6 pb-6 text-3xl">
|
||||
<p className="mr-4 font-semibold text-white">Explore More</p>
|
||||
<div
|
||||
className="mt-4 grid w-full grid-flow-dense gap-4"
|
||||
style={{ gridTemplateColumns: "repeat(auto-fill, minmax(256px, 4fr))" }}
|
||||
>
|
||||
{features.map((feature) => (
|
||||
<div
|
||||
key={feature._id}
|
||||
className="flex h-44 w-96 flex-col justify-between rounded-md border border-mineshaft-600 bg-mineshaft-800 p-4"
|
||||
>
|
||||
<div className="mt-0 text-lg text-mineshaft-100">{feature.name}</div>
|
||||
<div className="mb-4 mt-2 text-[15px] font-light text-mineshaft-300">
|
||||
{feature.description}
|
||||
</div>
|
||||
<div className="flex w-full items-center">
|
||||
<div className="text-[15px] font-light text-mineshaft-300">
|
||||
Setup time: 20 min
|
||||
</div>
|
||||
<a
|
||||
target="_blank"
|
||||
rel="noopener noreferrer"
|
||||
className="group ml-auto w-max cursor-default rounded-full border border-mineshaft-600 bg-mineshaft-900 py-2 px-4 text-sm text-mineshaft-300 hover:border-primary-500/80 hover:bg-primary-800/20 hover:text-mineshaft-200"
|
||||
href="https://infisical.com/docs/documentation/getting-started/kubernetes"
|
||||
>
|
||||
Learn more{" "}
|
||||
<FontAwesomeIcon
|
||||
icon={faArrowRight}
|
||||
className="pl-1.5 pr-0.5 duration-200 group-hover:pl-2 group-hover:pr-0"
|
||||
/>
|
||||
</a>
|
||||
</div>
|
||||
</div>
|
||||
))}
|
||||
</div>
|
||||
</div>
|
||||
<Modal
|
||||
isOpen={popUp.addNewWs.isOpen}
|
||||
onOpenChange={(isModalOpen) => {
|
||||
|
||||
@ -1,4 +1,5 @@
|
||||
import { faPlus } from "@fortawesome/free-solid-svg-icons";
|
||||
import Link from "next/link";
|
||||
import { faArrowUpRightFromSquare, faPlus } from "@fortawesome/free-solid-svg-icons";
|
||||
import { FontAwesomeIcon } from "@fortawesome/react-fontawesome";
|
||||
|
||||
import { useNotificationContext } from "@app/components/context/Notifications/NotificationProvider";
|
||||
@ -65,17 +66,24 @@ export const IdentitySection = withPermission(
|
||||
|
||||
return (
|
||||
<div className="mb-6 rounded-lg border border-mineshaft-600 bg-mineshaft-900 p-4">
|
||||
<div className="flex justify-between mb-8">
|
||||
<div className="flex justify-between mb-4">
|
||||
<p className="text-xl font-semibold text-mineshaft-100">
|
||||
Identities
|
||||
</p>
|
||||
<div className="flex justify-end w-full pr-4">
|
||||
<Link href="https://infisical.com/docs/documentation/platform/identities/overview">
|
||||
<span className="rounded-md px-4 py-2 w-max text-mineshaft-200 hover:text-white bg-mineshaft-600 border border-mineshaft-500 hover:bg-primary/10 hover:border-primary/40 duration-200 cursor-pointer">
|
||||
Documentation <FontAwesomeIcon icon={faArrowUpRightFromSquare} className="text-xs mb-[0.06rem] ml-1"/>
|
||||
</span>
|
||||
</Link>
|
||||
</div>
|
||||
<OrgPermissionCan
|
||||
I={OrgPermissionActions.Create}
|
||||
a={OrgPermissionSubjects.Identity}
|
||||
>
|
||||
{(isAllowed) => (
|
||||
<Button
|
||||
colorSchema="secondary"
|
||||
colorSchema="primary"
|
||||
type="submit"
|
||||
leftIcon={<FontAwesomeIcon icon={faPlus} />}
|
||||
onClick={() => handlePopUpOpen("identity")}
|
||||
|
||||
@ -89,7 +89,7 @@ export const OrgMembersSection = () => {
|
||||
|
||||
return (
|
||||
<div className="mb-6 rounded-lg border border-mineshaft-600 bg-mineshaft-900 p-4">
|
||||
<div className="flex justify-between mb-8">
|
||||
<div className="flex justify-between mb-4">
|
||||
<p className="text-xl font-semibold text-mineshaft-100">
|
||||
Members
|
||||
</p>
|
||||
@ -99,7 +99,7 @@ export const OrgMembersSection = () => {
|
||||
>
|
||||
{(isAllowed) => (
|
||||
<Button
|
||||
colorSchema="secondary"
|
||||
colorSchema="primary"
|
||||
type="submit"
|
||||
leftIcon={<FontAwesomeIcon icon={faPlus} />}
|
||||
onClick={() => handleAddMemberModal()}
|
||||
|
||||
@ -191,9 +191,9 @@ export const IdentityModal = ({
|
||||
</form>
|
||||
) : (
|
||||
<div className="flex flex-col space-y-4">
|
||||
<div>All identities in your organization are already added.</div>
|
||||
<div className="text-sm">All identities in your organization have already been added to this project.</div>
|
||||
<Link href={`/org/${currentWorkspace?.organization}/members`}>
|
||||
<Button variant="outline_bg">Create a new/another identities</Button>
|
||||
<Button variant="outline_bg">Create a new identity</Button>
|
||||
</Link>
|
||||
</div>
|
||||
)}
|
||||
|
||||
@ -1,4 +1,5 @@
|
||||
import { faPlus } from "@fortawesome/free-solid-svg-icons";
|
||||
import Link from "next/link";
|
||||
import { faArrowUpRightFromSquare, faPlus } from "@fortawesome/free-solid-svg-icons";
|
||||
import { FontAwesomeIcon } from "@fortawesome/react-fontawesome";
|
||||
|
||||
import { useNotificationContext } from "@app/components/context/Notifications/NotificationProvider";
|
||||
@ -61,17 +62,24 @@ export const IdentitySection = withProjectPermission(
|
||||
|
||||
return (
|
||||
<div className="mb-6 rounded-lg border border-mineshaft-600 bg-mineshaft-900 p-4">
|
||||
<div className="flex justify-between mb-8">
|
||||
<div className="flex justify-between items-center mb-4">
|
||||
<p className="text-xl font-semibold text-mineshaft-100">
|
||||
Identities
|
||||
</p>
|
||||
<div className="flex justify-end w-full pr-4">
|
||||
<Link href="https://infisical.com/docs/documentation/platform/identities/overview">
|
||||
<span className="rounded-md px-4 py-2 w-max text-mineshaft-200 hover:text-white bg-mineshaft-600 border border-mineshaft-500 hover:bg-primary/10 hover:border-primary/40 duration-200 cursor-pointer">
|
||||
Documentation <FontAwesomeIcon icon={faArrowUpRightFromSquare} className="text-xs mb-[0.06rem] ml-1"/>
|
||||
</span>
|
||||
</Link>
|
||||
</div>
|
||||
<ProjectPermissionCan
|
||||
I={ProjectPermissionActions.Create}
|
||||
a={ProjectPermissionSub.Identity}
|
||||
>
|
||||
{(isAllowed) => (
|
||||
<Button
|
||||
colorSchema="secondary"
|
||||
colorSchema="primary"
|
||||
type="submit"
|
||||
leftIcon={<FontAwesomeIcon icon={faPlus} />}
|
||||
onClick={() => handlePopUpOpen("identity")}
|
||||
|
||||
@ -254,7 +254,7 @@ export const MemberListTab = () => {
|
||||
|
||||
return (
|
||||
<div className="mb-6 rounded-lg border border-mineshaft-600 bg-mineshaft-900 p-4">
|
||||
<div className="flex justify-between mb-8">
|
||||
<div className="flex justify-between items-center mb-4">
|
||||
<p className="text-xl font-semibold text-mineshaft-100">
|
||||
Members
|
||||
</p>
|
||||
@ -264,7 +264,7 @@ export const MemberListTab = () => {
|
||||
>
|
||||
{(isAllowed) => (
|
||||
<Button
|
||||
colorSchema="secondary"
|
||||
colorSchema="primary"
|
||||
type="submit"
|
||||
leftIcon={<FontAwesomeIcon icon={faPlus} />}
|
||||
onClick={() => handlePopUpOpen("addMember")}
|
||||
|
||||
@ -6,6 +6,7 @@ import { useTranslation } from "react-i18next";
|
||||
import { faCheck, faCopy, faPlus, faTrashCan } from "@fortawesome/free-solid-svg-icons";
|
||||
import { FontAwesomeIcon } from "@fortawesome/react-fontawesome";
|
||||
import { yupResolver } from "@hookform/resolvers/yup";
|
||||
import { AxiosError } from "axios";
|
||||
import * as yup from "yup";
|
||||
|
||||
import { useNotificationContext } from "@app/components/context/Notifications/NotificationProvider";
|
||||
@ -160,10 +161,18 @@ export const AddServiceTokenModal = ({ popUp, handlePopUpToggle }: Props) => {
|
||||
});
|
||||
} catch (err) {
|
||||
console.error(err);
|
||||
createNotification({
|
||||
text: "Failed to create a service token",
|
||||
type: "error"
|
||||
});
|
||||
const axiosError = err as AxiosError
|
||||
if (axiosError?.response?.status === 401) {
|
||||
createNotification({
|
||||
text: "You do not have access to the selected environment/path",
|
||||
type: "error"
|
||||
});
|
||||
} else {
|
||||
createNotification({
|
||||
text: "Failed to create a service token",
|
||||
type: "error"
|
||||
});
|
||||
}
|
||||
}
|
||||
};
|
||||
|
||||
|
||||
@ -1,3 +1,7 @@
|
||||
import Link from "next/link";
|
||||
import { faArrowUpRightFromSquare } from "@fortawesome/free-solid-svg-icons";
|
||||
import { FontAwesomeIcon } from "@fortawesome/react-fontawesome";
|
||||
|
||||
import { Tab, TabList, TabPanel, Tabs } from "@app/components/v2";
|
||||
import { useWorkspace } from "@app/context";
|
||||
|
||||
@ -15,8 +19,18 @@ export const SecretApprovalPage = () => {
|
||||
|
||||
return (
|
||||
<div className="container mx-auto bg-bunker-800 text-white w-full h-full max-w-7xl px-6">
|
||||
<div className="my-6">
|
||||
<p className="text-3xl font-semibold text-gray-200">Secret Approvals</p>
|
||||
<div className="py-6 flex justify-between items-center">
|
||||
<div className="flex flex-col w-full">
|
||||
<h2 className="text-3xl font-semibold text-gray-200">Secret Approval Workflows</h2>
|
||||
<p className="text-bunker-300">Create approval policies for any modifications to secrets in sensitive environments and folders.</p>
|
||||
</div>
|
||||
<div className="flex justify-center w-max">
|
||||
<Link href="https://infisical.com/docs/documentation/platform/pr-workflows">
|
||||
<span className="rounded-md px-4 py-2 w-max text-mineshaft-200 hover:text-white bg-mineshaft-600 border border-mineshaft-500 hover:bg-primary/10 hover:border-primary/40 duration-200 cursor-pointer">
|
||||
Documentation <FontAwesomeIcon icon={faArrowUpRightFromSquare} className="text-xs mb-[0.06rem] ml-1"/>
|
||||
</span>
|
||||
</Link>
|
||||
</div>
|
||||
</div>
|
||||
<Tabs defaultValue={TabSection.ApprovalRequests}>
|
||||
<TabList>
|
||||
|
||||
@ -1,5 +1,6 @@
|
||||
import { Controller, useForm } from "react-hook-form";
|
||||
import { zodResolver } from "@hookform/resolvers/zod";
|
||||
import { AxiosError } from "axios";
|
||||
import { z } from "zod";
|
||||
|
||||
import { useNotificationContext } from "@app/components/context/Notifications/NotificationProvider";
|
||||
@ -78,12 +79,20 @@ export const CreateSecretImportForm = ({
|
||||
type: "success",
|
||||
text: "Successfully linked"
|
||||
});
|
||||
} catch (error) {
|
||||
console.log(error);
|
||||
createNotification({
|
||||
type: "error",
|
||||
text: "Failed to link secrets"
|
||||
});
|
||||
} catch (err) {
|
||||
console.error(err);
|
||||
const axiosError = err as AxiosError
|
||||
if (axiosError?.response?.status === 401) {
|
||||
createNotification({
|
||||
text: "You do not have access to the selected environment/path",
|
||||
type: "error"
|
||||
});
|
||||
} else {
|
||||
createNotification({
|
||||
type: "error",
|
||||
text: "Failed to link secrets"
|
||||
});
|
||||
}
|
||||
}
|
||||
};
|
||||
|
||||
|
||||
@ -108,11 +108,11 @@ export const FolderListView = ({
|
||||
key={id}
|
||||
className="flex group border-b border-mineshaft-600 hover:bg-mineshaft-700 cursor-pointer"
|
||||
>
|
||||
<div className="w-12 px-4 py-2 text-yellow-700 flex items-center">
|
||||
<div className="w-11 px-5 py-3 text-yellow-700 flex items-center">
|
||||
<FontAwesomeIcon icon={faFolder} />
|
||||
</div>
|
||||
<div
|
||||
className="flex-grow px-4 py-2 flex items-center"
|
||||
className="flex-grow px-4 py-3 flex items-center"
|
||||
role="button"
|
||||
tabIndex={0}
|
||||
onKeyDown={(evt) => {
|
||||
@ -122,7 +122,7 @@ export const FolderListView = ({
|
||||
>
|
||||
{name}
|
||||
</div>
|
||||
<div className="px-3 py-2 flex items-center space-x-4 border-l border-mineshaft-600">
|
||||
<div className="px-3 py-3 flex items-center space-x-4 border-l border-mineshaft-600">
|
||||
<ProjectPermissionCan
|
||||
I={ProjectPermissionActions.Edit}
|
||||
a={subject(ProjectPermissionSub.Secrets, { environment, secretPath })}
|
||||
|
||||
@ -270,22 +270,39 @@ export const SecretOverviewPage = () => {
|
||||
<p className="text-md text-bunker-300">
|
||||
Inject your secrets using
|
||||
<a
|
||||
className="mx-1 text-primary/80 hover:text-primary"
|
||||
className="ml-1 text-mineshaft-300 underline underline-offset-4 decoration-primary-800 hover:decoration-primary-600 hover:text-mineshaft-100 duration-200"
|
||||
href="https://infisical.com/docs/cli/overview"
|
||||
target="_blank"
|
||||
rel="noopener noreferrer"
|
||||
>
|
||||
Infisical CLI
|
||||
</a>
|
||||
or
|
||||
</a>,
|
||||
<a
|
||||
className="mx-1 text-primary/80 hover:text-primary"
|
||||
className="ml-1 text-mineshaft-300 underline underline-offset-4 decoration-primary-800 hover:decoration-primary-600 hover:text-mineshaft-100 duration-200"
|
||||
href="https://infisical.com/docs/documentation/getting-started/api"
|
||||
target="_blank"
|
||||
rel="noopener noreferrer"
|
||||
>
|
||||
Infisical API
|
||||
</a>
|
||||
,
|
||||
<a
|
||||
className="ml-1 text-mineshaft-300 underline underline-offset-4 decoration-primary-800 hover:decoration-primary-600 hover:text-mineshaft-100 duration-200"
|
||||
href="https://infisical.com/docs/sdks/overview"
|
||||
target="_blank"
|
||||
rel="noopener noreferrer"
|
||||
>
|
||||
Infisical SDKs
|
||||
</a>
|
||||
, and
|
||||
<a
|
||||
className="ml-1 text-mineshaft-300 underline underline-offset-4 decoration-primary-800 hover:decoration-primary-600 hover:text-mineshaft-100 duration-200"
|
||||
href="https://infisical.com/docs/documentation/getting-started/introduction"
|
||||
target="_blank"
|
||||
rel="noopener noreferrer"
|
||||
>
|
||||
more
|
||||
</a>.
|
||||
</p>
|
||||
</div>
|
||||
<div className="mt-8 flex items-center justify-between">
|
||||
@ -306,7 +323,7 @@ export const SecretOverviewPage = () => {
|
||||
<THead>
|
||||
<Tr className="sticky top-0 z-20 border-0">
|
||||
<Th className="sticky left-0 z-20 min-w-[20rem] border-b-0 p-0">
|
||||
<div className="flex items-center border-b border-r border-mineshaft-600 px-5 pt-4 pb-3.5">
|
||||
<div className="flex items-center border-b border-r border-mineshaft-600 px-5 pt-3.5 pb-3">
|
||||
Name
|
||||
<IconButton
|
||||
variant="plain"
|
||||
@ -326,7 +343,7 @@ export const SecretOverviewPage = () => {
|
||||
className="min-table-row min-w-[11rem] border-b-0 p-0 text-center"
|
||||
key={`secret-overview-${name}-${index + 1}`}
|
||||
>
|
||||
<div className="flex items-center justify-center border-b border-mineshaft-600 px-5 pt-3.5 pb-3">
|
||||
<div className="flex items-center justify-center border-b border-mineshaft-600 px-5 pt-3.5 pb-[0.83rem]">
|
||||
<button
|
||||
type="button"
|
||||
className="text-sm font-medium duration-100 hover:text-mineshaft-100"
|
||||
@ -382,7 +399,7 @@ export const SecretOverviewPage = () => {
|
||||
</Td>
|
||||
</Tr>
|
||||
)}
|
||||
{filteredFolderNames.map((folderName, index) => (
|
||||
{!isTableLoading && filteredFolderNames.map((folderName, index) => (
|
||||
<SecretOverviewFolderRow
|
||||
folderName={folderName}
|
||||
isFolderPresentInEnv={isFolderPresentInEnv}
|
||||
@ -391,7 +408,7 @@ export const SecretOverviewPage = () => {
|
||||
onClick={handleFolderClick}
|
||||
/>
|
||||
))}
|
||||
{userAvailableEnvs?.length > 0 ? (
|
||||
{!isTableLoading && (userAvailableEnvs?.length > 0 ? (
|
||||
filteredSecretNames.map((key, index) => (
|
||||
<SecretOverviewTableRow
|
||||
secretPath={secretPath}
|
||||
@ -407,7 +424,7 @@ export const SecretOverviewPage = () => {
|
||||
))
|
||||
) : (
|
||||
<PermissionDeniedBanner />
|
||||
)}
|
||||
))}
|
||||
</TBody>
|
||||
<TFoot>
|
||||
<Tr className="sticky bottom-0 z-10 border-0 bg-mineshaft-800">
|
||||
|
||||
@ -1,9 +1,12 @@
|
||||
import { useTranslation } from "react-i18next";
|
||||
import Link from "next/link";
|
||||
import {
|
||||
faArrowsSpin,
|
||||
faArrowUpRightFromSquare,
|
||||
faExclamationTriangle,
|
||||
faFolder,
|
||||
faInfoCircle,
|
||||
faPlus,
|
||||
faRotate,
|
||||
faTrash
|
||||
} from "@fortawesome/free-solid-svg-icons";
|
||||
@ -180,12 +183,21 @@ export const SecretRotationPage = withProjectPermission(
|
||||
|
||||
return (
|
||||
<div className="container mx-auto bg-bunker-800 text-white w-full h-full max-w-7xl px-6">
|
||||
<div className="my-6">
|
||||
<h2 className="text-3xl font-semibold text-gray-200">Secret Rotation</h2>
|
||||
<p className="text-bunker-300">Auto rotate secrets for better security</p>
|
||||
<div className="py-6 flex justify-between items-center">
|
||||
<div className="flex flex-col w-full">
|
||||
<h2 className="text-3xl font-semibold text-gray-200">Secret Rotation</h2>
|
||||
<p className="text-bunker-300">Stop manually rotating secrets and automate credential rotation.</p>
|
||||
</div>
|
||||
<div className="flex justify-center w-max">
|
||||
<Link href="https://infisical.com/docs/documentation/platform/secret-rotation/overview">
|
||||
<span className="rounded-md px-4 py-2 w-max text-mineshaft-200 hover:text-white bg-mineshaft-600 border border-mineshaft-500 hover:bg-primary/10 hover:border-primary/40 duration-200 cursor-pointer">
|
||||
Documentation <FontAwesomeIcon icon={faArrowUpRightFromSquare} className="text-xs mb-[0.06rem] ml-1"/>
|
||||
</span>
|
||||
</Link>
|
||||
</div>
|
||||
</div>
|
||||
<div className="mb-6">
|
||||
<div className="text-xl font-semibold text-gray-200 mb-2">Rotated Secrets</div>
|
||||
<div className="text-xl font-semibold text-gray-200 mb-2 mt-6">Rotated Secrets</div>
|
||||
<div className="flex flex-col space-y-2">
|
||||
<TableContainer>
|
||||
<Table>
|
||||
@ -322,7 +334,7 @@ export const SecretRotationPage = withProjectPermission(
|
||||
</TableContainer>
|
||||
</div>
|
||||
</div>
|
||||
<div className="text-xl font-semibold text-gray-200 mb-2">Infisical Rotation Providers</div>
|
||||
<div className="text-xl font-semibold text-gray-200 mb-2 mt-12">Infisical Rotation Providers</div>
|
||||
<div className="grid grid-cols-2 lg:grid-cols-3 2xl:grid-cols-4 gap-4">
|
||||
{isRotationProviderLoading &&
|
||||
Array.from({ length: 12 }).map((_, index) => (
|
||||
@ -331,7 +343,7 @@ export const SecretRotationPage = withProjectPermission(
|
||||
{!isRotationProviderLoading &&
|
||||
secretRotationProviders?.providers.map((provider) => (
|
||||
<div
|
||||
className="group relative cursor-pointer h-32 flex flex-row items-center rounded-md border border-mineshaft-600 bg-mineshaft-800 p-4"
|
||||
className="group relative cursor-pointer h-32 flex flex-row items-center rounded-md border border-mineshaft-600 bg-mineshaft-800 p-4 hover:border-primary/40 hover:bg-primary/10"
|
||||
key={`infisical-rotation-provider-${provider.name}`}
|
||||
tabIndex={0}
|
||||
role="button"
|
||||
@ -349,13 +361,21 @@ export const SecretRotationPage = withProjectPermission(
|
||||
<div className="ml-4 max-w-xs text-xl font-semibold text-gray-300 duration-200 group-hover:text-gray-200">
|
||||
{provider.title}
|
||||
</div>
|
||||
<div className="group-hover:opacity-100 transition-all opacity-0 absolute top-1 right-1">
|
||||
<div className="group-hover:opacity-100 transition-all opacity-0 absolute top-1 right-1.5">
|
||||
<Tooltip content={provider.description} sideOffset={10}>
|
||||
<FontAwesomeIcon icon={faInfoCircle} className="text-bunker-300" />
|
||||
<FontAwesomeIcon icon={faInfoCircle} className="text-primary" />
|
||||
</Tooltip>
|
||||
</div>
|
||||
</div>
|
||||
))}
|
||||
<Link href="https://github.com/Infisical/infisical/issues">
|
||||
<div className="group relative cursor-pointer h-32 flex flex-row items-center rounded-md border border-mineshaft-600 bg-mineshaft-800 p-4 hover:border-primary/40 hover:bg-primary/10">
|
||||
<FontAwesomeIcon icon={faPlus} className="text-gray-300 text-3xl pl-3 pr-2" />
|
||||
<div className="ml-4 max-w-xs text-xl font-semibold text-gray-300 duration-200 group-hover:text-gray-200">
|
||||
Request or create your own template
|
||||
</div>
|
||||
</div>
|
||||
</Link>
|
||||
</div>
|
||||
<CreateRotationForm
|
||||
isOpen={popUp.createRotation.isOpen}
|
||||
|
||||
@ -13,7 +13,7 @@ type: application
|
||||
# This is the chart version. This version number should be incremented each time you make changes
|
||||
# to the chart and its templates, including the app version.
|
||||
# Versions are expected to follow Semantic Versioning (https://semver.org/)
|
||||
version: 0.3.2
|
||||
version: 0.3.3
|
||||
# This is the version number of the application being deployed. This version number should be
|
||||
# incremented each time you make changes to the application. Versions are not expected to
|
||||
# follow Semantic Versioning. They should reflect the version the application is using.
|
||||
|
||||
@ -13,6 +13,7 @@ import (
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
ctrl "sigs.k8s.io/controller-runtime"
|
||||
)
|
||||
|
||||
const SERVICE_ACCOUNT_ACCESS_KEY = "serviceAccountAccessKey"
|
||||
@ -159,7 +160,13 @@ func (r *InfisicalSecretReconciler) CreateInfisicalManagedKubeSecret(ctx context
|
||||
Data: plainProcessedSecrets,
|
||||
}
|
||||
|
||||
err := r.Client.Create(ctx, newKubeSecretInstance)
|
||||
// Set InfisicalSecret instance as the owner and controller
|
||||
err := ctrl.SetControllerReference(&infisicalSecret, newKubeSecretInstance, r.Scheme)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
err = r.Client.Create(ctx, newKubeSecretInstance)
|
||||
if err != nil {
|
||||
return fmt.Errorf("unable to create the managed Kubernetes secret : %w", err)
|
||||
}
|
||||
|
||||